Digital certificates provide a means to digitally authenticate devices and individual users. An individual that wishes to send encrypted data obtains a digital certificate from a Certificate Authority (CA). The CA issues an encrypted digital certificate containing the applicant's public key and a variety of other identification information. The CA makes its own public key readily available. The recipient of the encrypted message uses the CA's public key to decode the digital certificate attached to the message, verifies it as issued by the CA, and then obtains the sender's public key and identification information held within the certificate. With this information, the recipient can send an encrypted reply. Public key infrastructure (PKI) is the enabler for managing digital certificates for IPSec VPN deployment. The most widely used format for digital certificates is X.509, which is supported by Cisco IOS.
In this blog, there are already having a couple of posts regarding using Symantec Digital Certificate to set up IPSec or SSL VPN for Check Point Firewalls, Juniper SRX firewalls, and Cisco IOS Routers. Here are some of posts lists:
- Using Symantec SSL PKI to Authenticate Cisco IOS IPSec VPN - HA Deployment
- Using PKI Build Route-Based IPSec VPN between Juniper SRX
- Certification based Cisco IPSec VPN Down caused by 'signature invalid'
- Troubleshooting Symantec Verisign SSL Certificates Issue on PKI VPN Tunnel between Juniper SRX Firewalls (Cont.)
- Using Symantec Verisign SSL Certificate for Check Point SSL VPN Mobile Access Portal
- Using Symantec Verisign PKI to authenticate Checkpoint Site-to-Site IPSec VPN
Using Symantec SSL PKI to Authenticate Cisco IOS IPSec VPN - HA Deployment has presented detail steps how you could use third party Certificate to authenticate your IPSEC IKE.
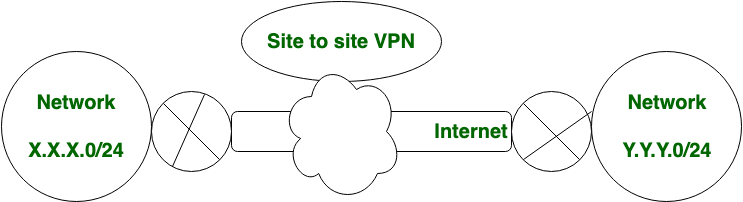
In this post I will summarize all configuration steps again and add a little more things into a new implementation. We will use a different CA in each peer gateway. The security gateways in all previous posts were using only one same CA - Symantec to authenticate IPSec IKE. We will use a different CA at each side this time.
Most steps are same as before, the only extra step we will need to add is to import your peer's CA certificate into a different Trustpoint.
R1(config)#crypto key generate rsa general-keys label R1.test.com modulus 2048 exportable
|
2. Create Trustpoint for Your Router
R1(config)#crypto pki trustpoint Verisign2015
R1(ca-trustpoint)#enrollment terminal R1(ca-trustpoint)#subject-name CN=R1.test.com,OU=IT,O=TT,C=CA,ST=Ontario,L=Markham R1(ca-trustpoint)#rsakeypair R1.test.com R1(ca-trustpoint)#fqdn R1.test.com R1(ca-trustpoint)#revocation-check none R1(ca-trustpoint)#exit |
3. Create CSR
R1(config)#crypto key generate rsa general-keys label R1.test.com modulus 2048 exportable The name for the keys will be: R1.test.com % The key modulus size is 2048 bits % Generating 2048 bit RSA keys, keys will be exportable... [OK] (elapsed time was 0 seconds) |
4. Submit CSR to Verisign and Retreive Signed Certificates
5. Install Intermediate / Root Certificate(s)
R1(config)#crypto pki authenticate Verisign2015 Enter the base 64 encoded CA certificate. End with a blank line or the word "quit" on a line by itself -----BEGIN CERTIFICATE----- MIIE0DCCBDmgAwIBAgIQJQzo4DBhLp8rifcFTXz4/TANgkqhkiG9w0BAQUFADBf MQswCQYDVQQGEwJVUzEXMBUGA1UEChMOVmVyaVNpZ24sIEluYy4xNzA1BgNVBAsT LkNsYXNzIDMgUHVibGljIFByaW1hcnkgQ2VydGlmaWNhdGlvbiBBdXRob3JpdHkw HhcNMDYxMTA4MDAwMDAwWhcNMjExMTA3MjM1OU5WjCByjELMAkGA1UEBhMCVVMx FzAVBgNVBAoTDlZlcmlTaWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2lnbiBUcnVz j+XTGoasjY5rw8+AatRIGCx7GS4wJRYjaHR0cDovL2xvZ28udmVyaXNpZ24uY29t L3ZzbG9nby5naWYwNAYIKwYBBQUHAQEKDAmMCQGCCsGAQUFBzABhhhodHRwOi8v b2NzcC52ZXJpc2lnbi5jb20wPgYDVR0lBDcwNQYIKwYBBQUHAwEGCCsGAQUFBwMC BggrBgEFBQcDAwYJYIZIAYb4QgQBBgpghkgBhvhFAQgBMA0GCSqGSIb3DQEBBQUA A4GBABMC3fjohgDyWvj4IAxZiGIHzs73Tvm7aGY5eE43U68ZhjTresY8g3JbT5K lCDDPLq9ZVTGr0SzEK0saz6r1we2uIFjxfleLuUqZ87NMwwq14lWAyMfs77oOghZ tOxFNfeKW/9mz1Cvxm1XjRl4t7mi0VfqH5pLr7rJjhJ+xr3/ -----END CERTIFICATE----- Trustpoint 'Verisign2015' is a subordinate CA and holds a non self signed cert Certificate has the following attributes: Fingerprint MD5: F91FFEE6 A36B9988 41D467DD E5F8977A Fingerprint SHA1: 32F30882 622B87CF 8856C63D B873DF08 53B4DD27 % Do you accept this certificate? [yes/no]: yes Trustpoint CA certificate accepted. % Certificate successfully imported |
6. Install Signed SSL Certificate on Cisco Router
R1(config)#crypto pki import Verisign2015 certificate
Enter the base 64 encoded certificate. End with a blank line or the word "quit" on a line by itself -----BEGIN CERTIFICATE----- MIIFgTCCBGmgAwIBAgIQKjCOdOIFbDkbDAxmz+KJjANBgkqhkiG9w0BAQUFADCB tTELMAkGA1UEBhMCVVMxFzAVBgNVBAoTlZlcmlTaWduLCBJbmMuMR8wHQYDVQQL ExZWZXJpU2lnbiBUcnVzdCBOZXR3b3JrMTsOQYDVQQLEzJUZXJtcyBvZiB1c2Ug LmNvbS9TVlJTZWN1cmVHMy5jmwwQwYDVR0gBDwwOjA4BgpghkgBhvhFAQc2MCow KAYIKwYBBQUHAgEWHGh0dHBzOi8vd3d3LnZlcmlzaWduLmNvbS9jcHMwHQYDVR0l BBYwFAYIKwYBBQUHAwEGCCsAQUFBwMCMB8GA1UdIwQYMBaAFA1EXBZTRMGCfh0g qyX0AWPYvnmlMHYGCCsGAQUBwEBBGowaDAkBggrBgEFBQcwAYYYaHR0cDovL29j c3AudmVyaXNpZ24uY29tMEAGCsGAQUFBzAChjRodHRwOi8vU1ZSU2VjdXJlLUcz LWFpYS52ZXJpc2lnbi5jb20vU1ZS2VjdXJlRzMuY2VyMA0GCSqGSIb3DQEBBQUA A4IBAQCpZzArqkr+wlVsmCpgCe5MPMUw/SpQj0gV3zIv5oeMvDfpJN+olwhqJI hOfPbPdr7dX/ep5JELJUDaAl5AFiON75PYJBtUcrnYuduzqdpY51MV0lUXsa7GP 0kR0ngAfTotDmE76iV5Uno/FiJtVTTM0ZqidPWihJprmtNUjH8BnLO8jA3Kwqw qvKgAXbJnBOrYb7gGVlPC6r4LPhX7B6dwDaoRDpliSvGBpGAEx6POIW5tD8lvUW RCZisxlco3oFnxJj6V7hm17dzfnELz49Nisa4vcgfW9eI3Z+2gtM0fT5/oVGDKb 4zRQ+2tLUF72B1WlfFZ4YFl7/m7 -----END CERTIFICATE----- % Router Certificate successfully imported |
7. Import Your Peer Intermediate / Root Certificate in a New TrustPoint
crypto pki trustpoint Customer
enrollment terminal revocation-check none ! R1(config)#crypto pki authenticate Customer Enter the base 64 encoded CA certificate. End with a blank line or the word "quit" on a line by itself -----BEGIN CERTIFICATE----- MIIE0DCCBDmgAwIBAgIQJQzo4DBhLp8rifcFTXz4/TANgkqhkiG9w0BAQUFADBf MQswCQYDVQQGEwJVUzEXMBUGA1UEChMOVmVyaVNpZ24sIEluYy4xNzA1BgNVBAsT LkNsYXNzIDMgUHVibGljIFByaW1hcnkgQ2VydGlmaWNhdGlvbiBBdXRob3JpdHkw HhcNMDYxMTA4MDAwMDAwWhcNMjExMTA3MjM1OU5WjCByjELMAkGA1UEBhMCVVMx FzAVBgNVBAoTDlZlcmlTaWduLCBJbmMuMR8wHQYDVQQLExZWZXJpU2lnbiBUcnVz j+XTGoasjY5rw8+AatRIGCx7GS4wJRYjaHR0cDovL2xvZ28udmVyaXNpZ24uY29t L3ZzbG9nby5naWYwNAYIKwYBBQUHAQEKDAmMCQGCCsGAQUFBzABhhhodHRwOi8v b2NzcC52ZXJpc2lnbi5jb20wPgYDVR0lBDcwNQYIKwYBBQUHAwEGCCsGAQUFBwMC BggrBgEFBQcDAwYJYIZIAYb4QgQBBgpghkgBhvhFAQgBMA0GCSqGSIb3DQEBBQUA A4GBABMC3fjohgDyWvj4IAxZiGIHzs73Tvm7aGY5eE43U68ZhjTresY8g3JbT5K lCDDPLq9ZVTGr0SzEK0saz6r1we2uIFjxfleLuUqZ87NMwwq14lWAyMfs77oOghZ tOxFNfeKW/9mz1Cvxm1XjRl4t7mi0VfqH5pLr7rJjhJ+xr3/ -----END CERTIFICATE----- Trustpoint 'Customer' is a subordinate CA and holds a non self signed cert Certificate has the following attributes: Fingerprint MD5: F91FFEE6 A36B9988 41D467DD E5F8977A Fingerprint SHA1: 32F30882 622B87CF 8856C63D B873DF08 53B4DD27 % Do you accept this certificate? [yes/no]: yes Trustpoint CA certificate accepted. % Certificate successfully imported |
8. Verify TrustPoint
R1#show crypto pki trustpoints
Trustpoint Verisign2015: Subject Name: cn=Symantec Class 3 Secure Server CA - G4 ou=Symantec Trust Network o=Symantec Corporation c=US Serial Number (hex): 513FB9743870B73440418D30930699FF Certificate configured. Trustpoint Customer: Subject Name: o=Customer Root Certification Authority c=CA st=Saskatchewan cn=Customer CA 2025 Serial Number (hex): 0082809023512072AD Certificate configured. |
R1#show crypto pki certificates
CA Certificate Status: Available Certificate Serial Number (hex): 0082809023512072AD Certificate Usage: General Purpose Issuer: o=Customer Root Certification Authority c=CA st=Saskatchewan cn=Customer CA 2025 Subject: o=Customer Root Certification Authority c=CA st=Saskatchewan cn=Customer CA 2025 Validity Date: start date: 10:55:50 EDT Mar 30 2015 end date: 10:55:50 EDT Mar 27 2025 Associated Trustpoints: Customer Storage: nvram:CustomerRootCerti#72ADCA.cer Certificate Status: Available Certificate Serial Number (hex): 44FC828CB095BC3BA7D553F4F4BF9EBA Certificate Usage: General Purpose Issuer: cn=Symantec Class 3 Secure Server CA - G4 ou=Symantec Trust Network o=Symantec Corporation c=US Subject: Name: R1.test.com cn=R1.test.com o=Giesecke & Devrient Systems Canada Inc l=Markham st=Ontario c=CA CRL Distribution Points: http://ss.symcb.com/ss.crl Validity Date: start date: 19:00:00 EST Dec 30 2015 end date: 18:59:59 EST Dec 30 2018 Associated Trustpoints: Verisign2015 Storage: nvram:SymantecClas#9EBA.cer CA Certificate Status: Available Certificate Serial Number (hex): 513FB9743870B73440418D30930699FF Certificate Usage: Signature Issuer: cn=VeriSign Class 3 Public Primary Certification Authority - G5 ou=(c) 2006 VeriSign Inc. - For authorized use only ou=VeriSign Trust Network o=VeriSign Inc. c=US Subject: cn=Symantec Class 3 Secure Server CA - G4 ou=Symantec Trust Network o=Symantec Corporation c=US CRL Distribution Points: http://s1.symcb.com/pca3-g5.crl Validity Date: start date: 20:00:00 EDT Oct 30 2013 end date: 19:59:59 EDT Oct 30 2023 Associated Trustpoints: Verisign2015 Storage: nvram:VeriSignClas#99FFCA.cer R1#show crypto isakmp sa detail Codes: C - IKE configuration mode, D - Dead Peer Detection K - Keepalives, N - NAT-traversal T - cTCP encapsulation, X - IKE Extended Authentication psk - Preshared key, rsig - RSA signature renc - RSA encryption IPv4 Crypto ISAKMP SA C-id Local Remote I-VRF Status Encr Hash Auth DH Lifetime Cap. 1073 19.26.116.141 20.19.60.26 ACTIVE aes sha2 rsig 14 20:28:46 D Engine-id:Conn-id = SW:73 IPv6 Crypto ISAKMP SA |
Note: Router's Full Configuration
R1#sh run Building configuration... Current configuration : 15460 bytes ! ! Last configuration change at 16:00:32 EST Fri Jan 8 2016 by john ! NVRAM config last updated at 16:01:19 EST Fri Jan 8 2016 by john ! NVRAM config last updated at 16:01:19 EST Fri Jan 8 2016 by john version 15.1 no service pad service tcp-keepalives-in service tcp-keepalives-out service timestamps debug datetime msec localtime show-timezone service timestamps log datetime msec localtime show-timezone service password-encryption service sequence-numbers ! hostname R1 ! boot-start-marker boot-end-marker ! ! logging buffered 409600 enable secret 5 $1$iNJa$8RiUCW5Tt9nPa5kMW.PT0/ ! ! ipc zone default association 1 no shutdown protocol sctp local-port 5000 local-ip 192.168.20.139 retransmit-timeout 300 10000 path-retransmit 10 assoc-retransmit 10 remote-port 5000 remote-ip 192.168.20.140 ! aaa new-model ! ! aaa authentication login default local group radius group tacacs+ aaa authentication enable default enable group radius group tacacs+ aaa authorization console aaa authorization exec default local group radius group tacacs+ aaa accounting exec default start-stop group tacacs+ aaa accounting commands 1 default stop-only group tacacs+ aaa accounting commands 5 default stop-only group tacacs+ aaa accounting commands 15 default stop-only group tacacs+ aaa accounting system default start-stop group tacacs+ ! ! ! ! ! aaa session-id common ! clock timezone EST -5 0 clock summer-time EDT recurring errdisable recovery cause bpduguard ! no ipv6 cef no ip source-route no ip gratuitous-arps ip cef ! ! ! ip dhcp bootp ignore ! ! no ip bootp server ip domain name gd.com ip name-server 8.8.8.8 ip name-server 8.8.4.4 login block-for 120 attempts 3 within 60 login on-failure log login on-success log ! multilink bundle-name authenticated ! crypto pki token default removal timeout 0 ! crypto pki trustpoint Verisign2015 enrollment terminal fqdn R1.test.com subject-name CN=R1.test.com,OU=IT,O=51Sec,C=CA,ST=Ontario,L=Markham revocation-check none rsakeypair R1.test.com ! crypto pki trustpoint Customer enrollment terminal revocation-check none ! ! crypto pki certificate chain Verisign2015 certificate 44FC828CB095BC3BA7D553F4F4BF9EBA 308204FD 308203E5 A0030201 02021044 FC828CB0 95BC3BA7 D553F4F4 BF9EBA30 0D06092A 864886F7 0D01010B 0500307E 310B3009 06035504 06130255 53311D30 1B060355 040A1314 53796D61 6E746563 20436F72 706F7261 74696F6E 311F301D 06035504 0B131653 796D616E 74656320 54727573 74204E65 74776F72 6B312F30 2D060355 04031326 53796D61 6E746563 20436C61 73732033 20536563 75726520 53657276 65722043 41202D20 4734301E 170D3135 31323331 30303030 30305A17 0D313831 32333032 33353935 395A3081 85310B30 09060355 04061302 43413110 300E0603 5504080C 074F6E74 6172696F 3110300E 06035504 070C074D 61726B68 616D312F 302D0603 55040A0C 26476965 7365636B 65202620 44657672 69656E74 20537973 74656D73 2043616E 61646120 496E6331 21301F06 03550403 0C18522D 544F5231 2D495053 65632D31 2E67692D 64652E63 6F6D3082 0122300D 06092A86 4886F70D 01010105 00038201 0F003082 010A0282 010100A7 FC4C44EB B6663518 6E3B5521 90241DE0 10F831FC B291F54D 2A5A0824 38C6BD63 526A4C01 8994442A 2C4543FB 58C29C01 7F820CEE 1CC89537 083FDAAD DE15CB65 76F3188F 8977B1E9 36FDFAC9 0DB9C7E1 A3781D41 DD0B8F78 5ED6BF2A 71862C17 06E5E2C4 C1505FA9 BB8E3A97 9226C8AD 6BA596A8 A717003A 57E3E3FC 68CADDD3 00715B72 5F729321 6CF031E0 614AB912 2A75B121 ED4FDC0B 80846343 F6AED8DF 911759A7 8A897F49 73B712FB 3720910E A9CBC536 6890BE1E EC0EF021 9A5674C6 CA33DDF6 DC663AFA FED35E2B AF9B0B4E DC11FB19 2832E02E F339A23F 99172FFF 460D480C 8BA25283 82FA8EAC 043DC71A 41ED7C32 AECC9B37 EF87BF06 F899F902 03010001 A382016D 30820169 30230603 551D1104 1C301A82 18522D54 4F52312D 49505365 632D312E 67692D64 652E636F 6D300906 03551D13 04023000 300E0603 551D0F01 01FF0404 030205A0 302B0603 551D1F04 24302230 20A01EA0 1C861A68 7474703A 2F2F7373 2E73796D 63622E63 6F6D2F73 732E6372 6C306106 03551D20 045A3058 30560606 67810C01 0202304C 30230608 2B060105 05070201 16176874 7470733A 2F2F642E 73796D63 622E636F 6D2F6370 73302506 082B0601 05050702 0230190C 17687474 70733A2F 2F642E73 796D6362 2E636F6D 2F727061 301D0603 551D2504 16301406 082B0601 05050703 0106082B 06010505 07030230 1F060355 1D230418 30168014 5F60CF61 9055DF84 43148A60 2AB2F57A F44318EF 30570608 2B060105 05070101 044B3049 301F0608 2B060105 05073001 86136874 74703A2F 2F73732E 73796D63 642E636F 6D302606 082B0601 05050730 02861A68 7474703A 2F2F7373 2E73796D 63622E63 6F6D2F73 732E6372 74300D06 092A8648 86F70D01 010B0500 03820101 00A9EA06 9A561D11 EB72E8C3 0FA4453C FFE376C8 E389BC20 B1A93B72 FA576E4F 5E598F26 F12E8636 77944F89 105C0802 B4D7D3EC E1E2F550 FC0DB830 B8336C29 407BC555 E36BB83B 83E29399 55379BCC A2AF808D 2A4CD262 9C1787C5 7CA2029B AAF5F6C0 57B0A869 4B822E2A 3355A2A5 F6F8D261 DBE46DB4 3782C9E8 186D739A 5865E249 FE9CA2CF 4D5F6974 4E959F51 8BB69E49 C4339211 978652F3 2A08858B 6859D3C5 30E3642C 4E670C9F C554C59A 648FF9E3 C1BAD434 062832B3 23B72814 60E8962E FA62F32A 38C2D432 57BD06D3 91DABA89 24A1B688 5409DA04 1EA0A93E CF4CA550 4A0378DF FF74B724 C48F8A43 FE5B36F3 C95C25A3 C488D881 8E40BE1F C0 quit certificate ca 513FB9743870B73440418D30930699FF 30820538 30820420 A0030201 02021051 3FB97438 70B73440 418D3093 0699FF30 0D06092A 864886F7 0D01010B 05003081 CA310B30 09060355 04061302 55533117 30150603 55040A13 0E566572 69536967 6E2C2049 6E632E31 1F301D06 0355040B 13165665 72695369 676E2054 72757374 204E6574 776F726B 313A3038 06035504 0B133128 63292032 30303620 56657269 5369676E 2C20496E 632E202D 20466F72 20617574 686F7269 7A656420 75736520 6F6E6C79 31453043 06035504 03133C56 65726953 69676E20 436C6173 73203320 5075626C 69632050 72696D61 72792043 65727469 66696361 74696F6E 20417574 686F7269 7479202D 20473530 1E170D31 33313033 31303030 3030305A 170D3233 31303330 32333539 35395A30 7E310B30 09060355 04061302 5553311D 301B0603 55040A13 1453796D 616E7465 6320436F 72706F72 6174696F 6E311F30 1D060355 040B1316 53796D61 6E746563 20547275 7374204E 6574776F 726B312F 302D0603 55040313 2653796D 616E7465 6320436C 61737320 33205365 63757265 20536572 76657220 4341202D 20473430 82012230 0D06092A 864886F7 0D010101 05000382 010F0030 82010A02 82010100 B2D805CA 1C742DB5 175639C5 4A520996 E84BD80C F1689F9A 422862C3 A530537E 5511825B 037A0D2F E17904C9 B4967719 81019459 F9BCF77A 9927822D B783DD5A 277FB203 7A9C5325 E9481F46 4FC89D29 F8BE7956 F6F7FDD9 3A68DA8B 4B823341 12C3C83C CCD6967A 84211A22 04032717 8B1C6861 930F0E51 80331DB4 B5CEEB7E D062ACEE B37B0174 EF6935EB CAD53DA9 EE9798CA 8DAA440E 25994A15 96A4CE6D 02541F2A 6A26E206 3A6348AC B44CD175 9350FF13 2FD6DAE1 C618F59F C9255DF3 003ADE26 4DB42909 CD0F3D23 6F164A81 16FBF283 10C3B8D6 D855323D F1BD0FBD 8C52954A 16977A52 2163752F 16F9C466 BEF5B509 D8FF2700 CD447C6F 4B3FB0F7 02030100 01A38201 63308201 5F301206 03551D13 0101FF04 08300601 01FF0201 00303006 03551D1F 04293027 3025A023 A021861F 68747470 3A2F2F73 312E7379 6D63622E 636F6D2F 70636133 2D67352E 63726C30 0E060355 1D0F0101 FF040403 02010630 2F06082B 06010505 07010104 23302130 1F06082B 06010505 07300186 13687474 703A2F2F 73322E73 796D6362 2E636F6D 306B0603 551D2004 64306230 60060A60 86480186 F8450107 36305230 2606082B 06010505 07020116 1A687474 703A2F2F 7777772E 73796D61 7574682E 636F6D2F 63707330 2806082B 06010505 07020230 1C1A1A68 7474703A 2F2F7777 772E7379 6D617574 682E636F 6D2F7270 61302906 03551D11 04223020 A41E301C 311A3018 06035504 03131153 796D616E 74656350 4B492D31 2D353334 301D0603 551D0E04 1604145F 60CF6190 55DF8443 148A602A B2F57AF4 4318EF30 1F060355 1D230418 30168014 7FD365A7 C2DDECBB F03009F3 4339FA02 AF333133 300D0609 2A864886 F70D0101 0B050003 82010100 5E945649 DD8E2D65 F5C13651 B603E3DA 9E7319F2 1F59AB58 7E6C2605 2CFA81D7 5C231722 2C3793F7 86EC85E6 B0A3FD1F E232A845 6FE1D9FB B9AFD270 A0324265 BF84FE16 2A8F3FC5 A6D6A393 7D43E974 21913528 F463E92E EDF7F55C 7F4B9AB5 20E90ABD E045100C 14949A5D A5E34B91 E8249B46 4065F422 72CD99F8 8811F5F3 7FE63382 E6A8C57E FED008E2 25580871 68E6CDA2 E614DE4E 52242DFD E5791353 E75E2F2D 4D1B6D40 15522BF7 87897812 416ED94D AA2D78D4 C22C3D08 5F87919E 1F0EB0DE 30526486 89AA9D66 9C0E760C 80F274D8 2AF8B83A CED7D60F 11BE6BAB 14F5BD41 A0226389 F1BA0F6F 2963662D 3FAC8C72 C5FBC7E4 D40FF23B 4F8C29C7 quit crypto pki certificate chain Customer certificate ca 0082809023512072AD 3082035D 30820245 A0030201 02020900 82809023 512072AD 300D0609 2A864886 F70D0101 0B050030 65311430 12060355 0403130B 53474920 43412032 30323531 15301306 03550408 130C5361 736B6174 63686577 616E310B 30090603 55040613 02434131 29302706 0355040A 13205347 4920526F 6F742043 65727469 66696361 74696F6E 20417574 686F7269 7479301E 170D3135 30333330 31343535 35305A17 0D323530 33323731 34353535 305A3065 31143012 06035504 03130B53 47492043 41203230 32353115 40130603 55040813 0C536173 6B617463 68657761 6E310B30 09060355 04061302 43413129 30270603 55040A13 20534749 20526F6F 74204365 72746966 69636174 696F6E20 41757468 6F726974 79308201 22300D06 092A8648 86F70D01 01010500 0382010F 00308201 0A028201 0100D005 9F2F2CF8 1C09E988 56577004 EECEE3A2 545AE573 7FE704C8 E1E6F722 CC4B745E 36C860A7 5E0590A1 7CE42928 3CD72621 7290E6FC 250F2E34 647D3DDE DF8306D8 6C28E3BD 3FD5FA92 D2B3406C 44DBD66C 2F69E895 861F93C6 A052143E F814245D 0C8DDE69 A2A0FAAC F337E69C 843426AB DD19E5C9 F60DB892 503414B9 1E678FE0 93652A7F E4FB8990 8894D38E 9795C691 F52D331C CA529033 CF90F4E3 98E7177E B69882EF CD2D9532 32180C7D 12C517A5 8C737C63 FED361C9 CEB8C8AD 59399CCF 3C7B1810 E0EA5CCA D774519D 76C0C50A 293322CF 44339523 6F8339F7 18CB539A 19D01136 70D46A13 21E50BBE C0C8B7DC 8955E88D 48DD7D31 1511986B B5DD0203 010001A3 10300E30 0C060355 1D130405 30030101 FF300D06 092A8648 86F70D01 010B0500 03820101 006302EE 40D8BADA 7D69A3C1 A7C03BE0 6BBD1410 B65679CC 7FAFC590 F0500E0A 1E44A841 B44F11C4 17E8DC94 124476C1 C7D352D3 5967554F 6571F067 D366622F C3A6ABAA 2FF2433C D9773D80 F99875BA 593D4F55 40194E12 AE01CC57 51E43C53 063EE6A0 580E837C B9C65739 E6BBC58F 752CFA34 7CE9BB45 4C494B49 FA90FBEB 1FE60AC2 7010EE86 644D1414 C402436B 26C58B9D FDA1D3DD 27DECDE7 123CDBB7 8C640943 3C56945C 9A7E4AA7 DDF70EDE 379BA01B 2E4D0A1D 624B8E8D BEC63755 529C9025 23632ABA 0365EAC2 A99C0B2F BB71C451 63BCD096 FA9501E3 C8976C2B 832E80D5 2FF61A7D 72215D6A 12E5F1CE 09722146 2AC182F4 FE00A902 62EE3D31 39 quit license udi pid CISCO1921/K9 sn FGL1529E0 ! ! archive log config logging enable logging size 200 notify syslog contenttype plaintext hidekeys ! no spanning-tree optimize bpdu transmission spanning-tree uplinkfast spanning-tree backbonefast vtp domain gd vtp mode transparent username localit privilege 15 secret 5 $1$P3q.$qQBIHNYDUCZH5y0XWTXzbq0 username localit autocommand show running username localadmin privilege 7 secret 5 $1$OgOX$owjSeZlPaU0A3K8DQJechd. username cadmin privilege 15 secret 5 $1$PE7E$Yyud3NJ2bl0OPSVkN0PQ// ! redundancy inter-device scheme standby VPNHA ! ! redundancy crypto ikev2 proposal aes-sha-256-proposal encryption aes-cbc-256 integrity sha256 group 14 ! crypto ikev2 policy ike2policy proposal aes-sha-256-proposal ! crypto ikev2 keyring VPN-KEYS peer Customer address 20.19.60.26 pre-shared-key local cisco123 pre-shared-key remote cisco123 ! ! crypto ikev2 keyring Test-KEYS peer Test address 19.26.116.137 pre-shared-key cisco123 ! ! ! crypto ikev2 profile Customer match identity remote address 20.19.60.26 255.255.255.255 identity local address 19.26.116.141 authentication local pre-share authentication remote pre-share keyring VPN-KEYS ! crypto ikev2 profile Test match identity remote address 0.0.0.0 match identity remote address 19.26.116.137 255.255.255.255 identity local address 19.26.116.141 authentication local pre-share authentication remote pre-share keyring Test-KEYS ! ! ! ip ssh time-out 10 ip ssh logging events ip ssh version 2 ! track 1 interface GigabitEthernet0/0 line-protocol ! track 2 interface GigabitEthernet0/1 line-protocol ! class-map type port-filter match-any TCP23 match port tcp 23 ! ! policy-map type port-filter FILTERTCP23 class TCP23 drop log ! ! ! crypto isakmp policy 1 encr aes 256 hash sha256 group 14 crypto isakmp key cisco123 address 20.19.60.26 no-xauth crypto isakmp keepalive 10 crypto isakmp aggressive-mode disable ! ! crypto ipsec transform-set mysec esp-aes 256 esp-sha256-hmac ! crypto map vpn 10 ipsec-isakmp set peer 20.19.60.26 set transform-set mysec set pfs group14 match address Gand reverse-route ! ! ! ! ! interface Embedded-Service-Engine0/0 no ip address shutdown ! interface GigabitEthernet0/0 ip address 19.26.116.139 255.255.255.192 ip accounting output-packets standby 199 ip 19.26.116.141 standby 199 priority 105 standby 199 preempt standby 199 name VPNHA standby 199 track 2 decrement 10 duplex auto speed auto crypto map vpn redundancy VPNHA stateful ! interface GigabitEthernet0/1 ip address 192.168.20.139 255.255.255.0 standby 200 ip 192.168.20.141 standby 200 priority 105 standby 200 preempt standby 200 name CLIENTS standby 200 track 1 decrement 10 duplex auto speed auto ! ip forward-protocol nd ! no ip http server no ip http secure-server ! ip route 0.0.0.0 0.0.0.0 19.26.116.161 ! ip access-list extended Gand permit ip host 192.168.20.25 172.21.90.0 0.0.1.255 permit icmp host 192.168.20.25 172.21.90.0 0.0.1.255 ! logging trap debugging logging 10.9.20.33 access-list 101 permit ip 10.94.200.0 0.0.0.255 any log access-list 101 permit ip 19.26.116.0 0.0.0.255 any log access-list 110 permit ip host 192.168.20.25 host 172.21.91.37 access-list 110 permit ip host 172.21.91.37 host 192.168.20.25 ! ! ! ! ! ! ! ! control-plane ! ! privilege exec level 7 show configuration privilege exec level 7 show banner motd ^C **************************************************************** * This is a private computing facility. * * Unauthorized use of this device is strictly prohibited. * * Violators will be prosecuted to the maximum extent possible. * * * * TACACS+/RADIUS Authentication and Authorization are in place.* * All actions/commands are monitored and recorded. * * By using the network you expressly consent to such * * monitoring and recording. * **************************************************************** ^C ! line con 0 exec-timeout 5 0 logging synchronous login authentication CONAUTH stopbits 1 line aux 0 line 2 no activation-character no exec transport preferred none transport input all transport output pad telnet rlogin lapb-ta mop udptn v120 ssh stopbits 1 line vty 0 4 access-class 101 in exec-timeout 5 0 logging synchronous login authentication VTYAUTH transport input ssh line vty 5 15 access-class 101 in exec-timeout 5 0 absolute-timeout 15 logging synchronous login authentication VTYAUTH transport input ssh ! scheduler allocate 20000 1000 ntp server 0.ca.pool.ntp.org ntp server 1.ca.pool.ntp.org ntp server 2.ca.pool.ntp.org ntp server 3.ca.pool.ntp.org end |
Here are some summarize for all steps from Cisco forum post:
"
In general what you need to do is (typical scenario)
On all systems (including CA)
- Setup correct time (NTP highly recommended)
- config hostname and domain name.
- generate RSA keys. private and public they will be used to encrypt/sign certificates.
On ASA/IOS device you wish to enroll:
- configured trustpoint with what-need-you (crl, enrollemtn method etc etc).
- you authenticate a trustpoint by introducing CA who issues your certificate.
- you then generate CSR or enroll via SCEP.
- You download/import certificate from CA. It is signed by public key of CA.
Your certification is normally two parts - your identity certificate, trusted third party certificate who issued you your certificate.
It all boils down to who you trust, if you want one side to use entrust and other to use verisign, you need to have appropriate CA authenticated in you device.
Now all modern operatin system provide you will a list of well known trusted third parties in your certificate store. Which is why when you as user going to "my_internet_bank.com" don't need to trust anything.
This is not the case on ASA or IOS, there is no default list of trusted third parties, all has to be done manually.
"





No comments:
Post a Comment