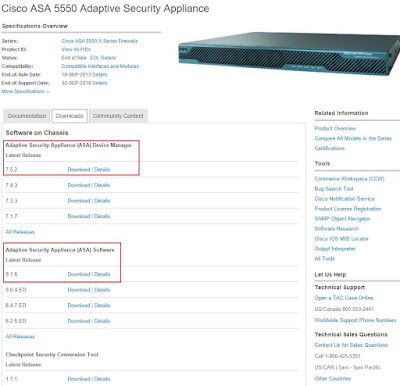
1. Download Software from Cisco Website
You may need to use your ASA's serial number to find out latest support IOS version and ASDM version from Cisco support site. CCO account will be needed as well.
You will have two files for this upgrade:
- asa916-k8.bin - for ASA IOS, about 26M
- asdm-752.bin - for ASA's ASDM , about 25M
Configure management interface 0/0 with ip address 10.1.13. Also you will need to set up proper nameif and security level to enable this port. After all configured, do not forget to write all configuration to flash card.
ciscoasa(config)# int management 0/0
ciscoasa(config-if)# ip address 10.1.1.1 255.255.255.0 ciscoasa(config-if)# management-only ciscoasa(config-if)# nameif management INFO: Security level for "management" set to 0 by default. ciscoasa(config-if)# security-level 100 ciscoasa(config-if)# ciscoasa(config)# wr Building configuration... Cryptochecksum: 2f6ce793 14d757a0 d226a8da db8c3472 2582 bytes copied in 3.580 secs (860 bytes/sec) [OK] |
3. TFTP configuration
Set up your computer with ip address 10.1.1.2, which is same network as your ASA management interface. Start your TFTP application with proper configuration. I am using Tftpd32 by Ph.Jounin to set up my tftp server. Make sure you are selecting right server interface if you are having multiple network interfaces. I have put downloaded IOS 9.1.6 version and ASDM into d;\ios foler.
After connected ASA's management interface with your tftp server, verify the connectivity from ASA to your TFTP server by ping-ing tftp server ip 10.1.1.2. You may need to disable your local firewall on your tftp server machine.
ciscoasa(config)# ping 10.1.1.2
Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.1.1.2, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/1 ms |
4. Copy both IOS and ASDM files from TFTP to ASA Flash
ciscoasa(config)# copy tftp: flash:
Address or name of remote host []? 10.1.1.2 Source filename []? asa916-k8.bin Destination filename [asa916-k8.bin]? Accessing tftp://10.1.1.2/asa916-k8.bin...!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! Writing file disk0:/asa916-k8.bin... !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! 27150336 bytes copied in 30.390 secs (905011 bytes/sec) ciscoasa(config)# copy tftp: flash: Address or name of remote host [10.1.1.2]? Source filename [asa916-k8.bin]? asdm-752.bin Destination filename [asdm-752.bin]? Accessing tftp://10.1.1.2/asdm-752.bin...!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! Writing file disk0:/asdm-752.bin... !!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! 25627616 bytes copied in 28.700 secs (915272 bytes/sec) |
5. Boot ASA with new IOS and load new ASDM image
ciscoasa(config)# boot system disk0:/asa916-k8.bin
ciscoasa(config)# asdm image disk0:/asdm-752.bin ciscoasa(config)# wr Building configuration... Cryptochecksum: bab14ac0 c6d4808b 1c61875d 96255622 2646 bytes copied in 3.720 secs (882 bytes/sec) [OK] ciscoasa(config)# ciscoasa(config)# reload Proceed with reload? [confirm] ciscoasa(config)# *** *** --- START GRACEFUL SHUTDOWN --- Shutting down isakmp Shutting down webvpn Shutting down File system *** *** --- SHUTDOWN NOW --- Process shutdown finished Rebooting..... Restarting system. |
Following output is from booting console:
Booting system, please wait...
CISCO SYSTEMS Embedded BIOS Version 1.0(11)5 08/28/08 15:11:51.82 Low Memory: 631 KB High Memory: 3968 MB PCI Device Table. Bus Dev Func VendID DevID Class Irq 00 00 00 8086 2578 Host Bridge 00 01 00 8086 2579 PCI-to-PCI Bridge 00 03 00 8086 257B PCI-to-PCI Bridge 00 1C 00 8086 25AE PCI-to-PCI Bridge 00 1D 00 8086 25A9 Serial Bus 11 00 1D 01 8086 25AA Serial Bus 10 00 1D 04 8086 25AB System 00 1D 05 8086 25AC IRQ Controller 00 1D 07 8086 25AD Serial Bus 9 00 1E 00 8086 244E PCI-to-PCI Bridge 00 1F 00 8086 25A1 ISA Bridge 00 1F 02 8086 25A3 IDE Controller 11 00 1F 03 8086 25A4 Serial Bus 5 00 1F 05 8086 25A6 Audio 5 02 01 00 8086 1075 Ethernet 11 03 01 00 177D 0003 Encrypt/Decrypt 9 03 02 00 8086 1079 Ethernet 9 03 02 01 8086 1079 Ethernet 9 03 03 00 8086 1079 Ethernet 9 03 03 01 8086 1079 Ethernet 9 04 02 00 8086 1209 Ethernet 11 04 03 00 8086 1209 Ethernet 5 Evaluating BIOS Options ... Launch BIOS Extension to setup ROMMON Cisco Systems ROMMON Version (1.0(11)5) #0: Thu Aug 28 15:23:50 PDT 2008 Platform ASA5550 Use BREAK or ESC to interrupt boot. Use SPACE to begin boot immediately. Launching BootLoader... Boot configuration file contains 1 entry. Loading disk0:/asa916-k8.bin... Booting... Platform ASA5550 Loading... IO memory blocks requested from bigphys 32bit: 78436 dosfsck 2.11, 12 Mar 2005, FAT32, LFN Starting check/repair pass. Starting verification pass. /dev/hda1: 130 files, 11109/31180 clusters dosfsck(/dev/hda1) returned 0 Processor memory 3166699520, Reserved memory: 157286400 Total SSMs found: 1 SSM-4GE-INC, SN JAF1335BEME, HW ver 1.0, FW ver 1.0(0)8 Total NICs found: 12 mcwa i82557 Ethernet at irq 11 MAC: 0023.ebc4.364c mcwa i82557 Ethernet at irq 5 MAC: 0000.0001.0001 i82547GI rev00 Gigabit Ethernet @ irq11 dev 1 index 05 MAC: 0000.0001.0002 i82546GB rev03 Gigabit Ethernet @ irq09 dev 2 index 03 MAC: 0023.ebc4.364b i82546GB rev03 Gigabit Ethernet @ irq09 dev 2 index 02 MAC: 0023.ebc4.364a i82546GB rev03 Gigabit Ethernet @ irq09 dev 3 index 01 MAC: 0023.ebc4.3649 i82546GB rev03 Gigabit Ethernet @ irq09 dev 3 index 00 MAC: 0023.ebc4.3648 VCS7380 Gigabit Ethernet @ index 07 MAC: 0026.0b31.564c VCS7380 Gigabit Ethernet @ index 08 MAC: 0026.0b31.564d VCS7380 Gigabit Ethernet @ index 09 MAC: 0026.0b31.564e VCS7380 Gigabit Ethernet @ index 10 MAC: 0026.0b31.564f VCS7380 Gigabit Ethernet @ index 11 MAC: 0000.0003.0002 INFO: Unable to read cluster interface-mode from flash Writing default mode "None" to flash Verify the activation-key, it might take a while... Running Permanent Activation Key: 0xd41ee978 0xb495d93b 0x48934db8 0xbd7c2014 0xc502138f Licensed features for this platform: Maximum Physical Interfaces : Unlimited perpetual Maximum VLANs : 400 perpetual Inside Hosts : Unlimited perpetual Failover : Active/Active perpetual Encryption-DES : Enabled perpetual Encryption-3DES-AES : Enabled perpetual Security Contexts : 2 perpetual GTP/GPRS : Disabled perpetual AnyConnect Premium Peers : 2 perpetual AnyConnect Essentials : Disabled perpetual Other VPN Peers : 5000 perpetual Total VPN Peers : 5000 perpetual Shared License : Disabled perpetual AnyConnect for Mobile : Disabled perpetual AnyConnect for Cisco VPN Phone : Disabled perpetual Advanced Endpoint Assessment : Disabled perpetual UC Phone Proxy Sessions : 2 perpetual Total UC Proxy Sessions : 2 perpetual Botnet Traffic Filter : Disabled perpetual Intercompany Media Engine : Disabled perpetual Cluster : Disabled perpetual This platform has an ASA 5550 VPN Premium license. Encryption hardware device : Cisco ASA-55xx on-board accelerator (revision 0x0) Boot microcode : CN1000-MC-BOOT-2.00 SSL/IKE microcode : CNLite-MC-SSLm-PLUS-2_05 IPSec microcode : CNlite-MC-IPSECm-MAIN-2.09 Cisco Adaptive Security Appliance Software Version 9.1(6) ****************************** Warning ******************************* This product contains cryptographic features and is subject to United States and local country laws governing, import, export, transfer, and use. Delivery of Cisco cryptographic products does not imply third-party authority to import, export, distribute, or use encryption. Importers, exporters, distributors and users are responsible for compliance with U.S. and local country laws. By using this product you agree to comply with applicable laws and regulations. If you are unable to comply with U.S. and local laws, return the enclosed items immediately. A summary of U.S. laws governing Cisco cryptographic products may be found at: http://www.cisco.com/wwl/export/crypto/tool/stqrg.html If you require further assistance please contact us by sending email to export@cisco.com. ******************************* Warning ******************************* This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/) Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved. Copyright (c) 1998-2011 The OpenSSL Project. All rights reserved. This product includes software developed at the University of California, Irvine for use in the DAV Explorer project (http://www.ics.uci.edu/~webdav/) Copyright (c) 1999-2005 Regents of the University of California. All rights reserved. Busybox, version 1.16.1, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA Busybox comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. DOSFSTOOLS, version 2.11, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 675 Mass Ave, Cambridge, MA 02139 DOSFSTOOLS comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. grub, version 0.94, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 grub comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. libgcc, version 4.3, Copyright (C) 2007 Free Software Foundation, Inc. libgcc comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. libstdc++, version 4.3, Copyright (C) 2007 Free Software Foundation, Inc. libstdc++ comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. Linux kernel, version 2.6.29.6, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA Linux kernel comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. module-init-tools, version 3.10, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA module-init-tools comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. numactl, version 2.0.3, Copyright (C) 2008 Author: Andi Kleen, SUSE Labs Version 2.0.0 by Cliff Wickman, Chritopher Lameter and Lee Schermerhorn numactl comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. pciutils, version 3.1.4, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA pciutils comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. readline, version 5.2, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111 USA readline comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. udev, version 146, Copyright (C) 1989, 1991 Free Software Foundation, Inc. 51 Franklin St, Fifth Floor, Boston, MA 02110-1301 USA udev comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. util-linux, version 2.16.1, Copyright (C) 1989, 1991 Free Software Foundation, Inc. The following components, built for inclusion in Busybox. The following components from util-linux come with ABSOLUTELY NO WARRANTY. fdisk: Copyright (C) 1992 A. V. Le Blanc (LeBlanc@mcc.ac.uk) Copyright (C) 2001,2002 Vladimir Oleynik <dzo@simtreas.ru> (initial bb port) dmesg: Copyright 2006 Rob Landley <rob@landley.net> Copyright 2006 Bernhard Reutner-Fischer <rep.nop@aon.at> mkswap: Copyright 2006 Rob Landley <rob@landley.net> mount: Copyright (C) 1995, 1996 by Bruce Perens <bruce@pixar.com>. Copyright (C) 1999-2004 by Erik Andersen <andersen@codepoet.org> Copyright (C) 2005-2006 by Rob Landley <rob@landley.net> umount: Copyright (C) 1999-2004 by Erik Andersen <andersen@codepoet.org> Copyright (C) 2005 by Rob Landley <rob@landley.net> This is free software, and you are welcome to redistribute it under the General Public License v.2 (http://www.gnu.org/licenses/gpl-2.0.html) See User Manual (''Licensing'') for details. Cisco Adapative Security Appliance Software, version 9.1, Copyright (c) 1996-2015 by Cisco Systems, Inc. Certain components of Cisco ASA Software, Version 9.1 are licensed under the GNU Lesser Public License (LGPL) Version 2.1. The software code licensed under LGPL Version 2.1 is free software that comes with ABSOLUTELY NO WARRANTY. You can redistribute and/or modify such LGPL code under the terms of LGPL Version 2.1 (http://www.gnu.org/licenses/lgpl-2.1.html). See User Manual for licensing details. Restricted Rights Legend Use, duplication, or disclosure by the Government is subject to restrictions as set forth in subparagraph (c) of the Commercial Computer Software - Restricted Rights clause at FAR sec. 52.227-19 and subparagraph (c) (1) (ii) of the Rights in Technical Data and Computer Software clause at DFARS sec. 252.227-7013. Cisco Systems, Inc. 170 West Tasman Drive San Jose, California 95134-1706 Reading from flash... ! REAL IP MIGRATION: WARNING In this version access-lists used in 'access-group', 'class-map', 'dynamic-filter classify-list', 'aaa match' will be migrated from using IP address/ports as seen on interface, to their real values. If an access-list used by these features is shared with per-user ACL then the original access-list has to be recreated. INFO: Note that identical IP addresses or overlapping IP ranges on different interfaces are not detectable by automated Real IP migration. If your deployment contains such scenarios, please verify your migrated configuration is appropriate for those overlapping addresses/ranges. Please also refer to the ASA 8.3 migration guide for a complete explanation of the automated migration process. INFO: MIGRATION - Saving the startup configuration to file INFO: MIGRATION - Startup configuration saved to file 'flash:8_2_1_0_startup_cfg.sav' *** Output from config line 4, "ASA Version 8.2(1) " . Cryptochecksum (unchanged): 46743c59 c0bc15d3 43afde7f 39783981 Real IP migration logs: No ACL was changed as part of Real-ip migration INFO: Power-On Self-Test in process. ........................................................... INFO: Power-On Self-Test complete. INFO: MIGRATION - Saving the startup errors to file 'flash:upgrade_startup_errors_201512181715.log' Type help or '?' for a list of available commands. ciscoasa> en Password: ciscoasa# ciscoasa# ciscoasa# conf t ciscoasa(config)# ***************************** NOTICE ***************************** Help to improve the ASA platform by enabling anonymous reporting, which allows Cisco to securely receive minimal error and health information from the device. To learn more about this feature, please visit: http://www.cisco.com/go/smartcall Would you like to enable anonymous error reporting to help improve the product? [Y]es, [N]o, [A]sk later: n In the future, if you would like to enable this feature, issue the command "call-home reporting anonymous". Please remember to save your configuration. |
6. Verify ASDM
Configure ASA to allow ASDM client network to access ASA's management port.
ciscoasa(config)# http server enable
ciscoasa(config)# http 10.1.1.0 255.255.255.0 management ciscoasa(config)# wr Building configuration... Cryptochecksum: d719ed8f 2578f2f0 20d50a04 fe506e2b 3754 bytes copied in 3.190 secs (1251 bytes/sec) [OK] ciscoasa(config)# |
Open your browser with url http://10.1.1.1, you should get following screen to install ASDM launcher.
Here is log in window from ASDM Launcher. If it asks username and password, just leave it empty and press enter.
Reference:
- PIX/ASA: Upgrade a Software Image using ASDM or CLI Configuration Example
- How To Upgrade Cisco ASA Software And ASDM









No comments:
Post a Comment