Other examples to troubleshoot IPSec VPN issue:
- Troubleshooting Cisco IPSec Site to Site VPN - "reason: Unknown delete reason!" after Phase 1 Completed
- Troubleshooting Cisco IPSec Site to Site VPN - "IPSec policy invalidated proposal with error 32"
- Troubleshooting Cisco IPSec Site to Site VPN - "QM Rejected"
Symptom:
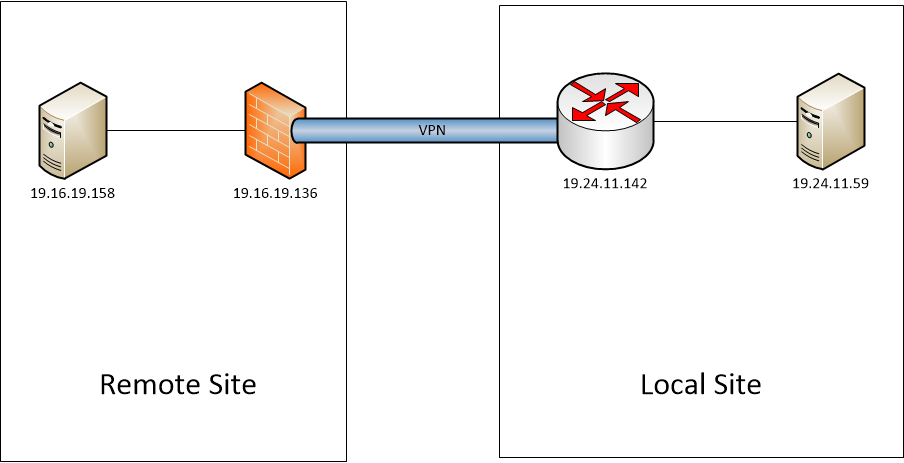
When traffic initiated from remote site server 19.16.19.158 to local server 19.24.11.59, vpn tunnel can be built without problem. But if Traffic initiated from local site, tunnel failed and SA deleted right away after tunnel phase 1 completed.
Configuration :
crypto isakmp policy 2 encr aes 256 authentication pre-share group 5 crypto isakmp key xxxxxxxxx address 19.16.19.136 crypto isakmp aggressive-mode disable crypto ipsec transform-set Set1 esp-aes 256 esp-sha-hmac crypto map vpn 30 ipsec-isakmp set peer 19.16.19.136 set transform-set Set1 set pfs group2 match address VPN-Test ip access-list extended VPN-Test permit ip host 19.24.11.59 host 19.16.19.158 |
When traffic initiated from local server 19.24.11.59 to remote server 19.16.19.158, VPN Tunnel was not up based on above configuration.
Troubleshooting:
Troubleshooting command on Cisco router:
- Debug Crypto ISAKMP
- Debug Crypto IPSEC
- Terminal Monitor
Following is the terminal logs:
R1-IPSEC1# 031993: May 20 12:00:33.442 EDT: IPSEC(sa_request): , (key eng. msg.) OUTBOUND local= 19.24.11.142:500, remote= 19.16.19.136:500, local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1), remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1), protocol= ESP, transform= esp-aes 256 esp-sha-hmac (Tunnel), lifedur= 3600s and 4608000kb, spi= 0x0(0), conn_id= 0, keysize= 256, flags= 0x0 031994: May 20 12:00:33.442 EDT: ISAKMP:(0): SA request profile is (NULL) 031995: May 20 12:00:33.442 EDT: ISAKMP: Created a peer struct for 19.16.19.136, peer port 500 031996: May 20 12:00:33.442 EDT: ISAKMP: New peer created peer = 0x313D5AA8 peer_handle = 0x80000049 031997: May 20 12:00:33.442 EDT: ISAKMP: Locking peer struct 0x313D5AA8, refcount 1 for isakmp_initiator 031998: May 20 12:00:33.446 EDT: ISAKMP: local port 500, remote port 500 031999: May 20 12:00:33.446 EDT: ISAKMP: set new node 0 to QM_IDLE 032000: May 20 12:00:33.446 EDT: ISAKMP:(0):insert sa successfully sa = 2A271B9C 032001: May 20 12:00:33.446 EDT: %CRYPTO-5-IKMP_AG_MODE_DISABLED: Unable to initiate or respond to Aggressive Mode while disabled 032002: May 20 12:00:33.446 EDT: ISAKMP:(0):Can not start Aggressive mode, trying Main mode. 032003: May 20 12:00:33.446 EDT: ISAKMP:(0):found peer pre-shared key matching 19.16.19.136 032004: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-rfc3947 ID 032005: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-07 ID 032006: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-03 ID 032007: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-02 ID 032008: May 20 12:00:33.446 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_MM 032009: May 20 12:00:33.446 EDT: ISAKMP:(0):Old State = IKE_READY New State = IKE_I_MM1 032010: May 20 12:00:33.446 EDT: ISAKMP:(0): beginning Main Mode exchange 032011: May 20 12:00:33.446 EDT: ISAKMP:(0): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) MM_NO_STATE 032012: May 20 12:00:33.446 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet. 032013: May 20 12:00:33.474 EDT: ISAKMP (0): received packet from 19.16.19.136 dport 500 sport 500 Global (I) MM_NO_STATE 032014: May 20 12:00:33.474 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032015: May 20 12:00:33.474 EDT: ISAKMP:(0):Old State = IKE_I_MM1 New State = IKE_I_MM2 032016: May 20 12:00:33.474 EDT: ISAKMP:(0): processing SA payload. message ID = 0 032017: May 20 12:00:33.474 EDT: ISAKMP:(0): processing vendor id payload 032018: May 20 12:00:33.474 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch 032019: May 20 12:00:33.474 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947 032020: May 20 12:00:33.474 EDT: ISAKMP:(0): processing vendor id payload 032021: May 20 12:00:33.474 EDT: ISAKMP:(0): processing IKE frag vendor id payload 032022: May 20 12:00:33.474 EDT: ISAKMP:(0):Support for IKE Fragmentation not enabled 032023: May 20 12:00:33.474 EDT: ISAKMP:(0):found peer pre-shared key matching 19.16.19.136 032024: May 20 12:00:33.478 EDT: ISAKMP:(0): local preshared key found 032025: May 20 12:00:33.478 EDT: ISAKMP : Scanning profiles for xauth ... 032026: May 20 12:00:33.478 EDT: ISAKMP:(0):Checking ISAKMP transform 1 against priority 1 policy 032027: May 20 12:00:33.478 EDT: ISAKMP: encryption 3DES-CBC 032028: May 20 12:00:33.478 EDT: ISAKMP: hash SHA 032029: May 20 12:00:33.478 EDT: ISAKMP: default group 2 032030: May 20 12:00:33.478 EDT: ISAKMP: auth pre-share 032031: May 20 12:00:33.478 EDT: ISAKMP: life type in seconds 032032: May 20 12:00:33.478 EDT: ISAKMP: life duration (basic) of 3600 032033: May 20 12:00:33.478 EDT: ISAKMP:(0):atts are acceptable. Next payload is 0 032034: May 20 12:00:33.478 EDT: ISAKMP:(0):Acceptable atts:actual life: 0 032035: May 20 12:00:33.478 EDT: ISAKMP:(0):Acceptable atts:life: 0 032036: May 20 12:00:33.478 EDT: ISAKMP:(0):Basic life_in_seconds:3600 032037: May 20 12:00:33.478 EDT: ISAKMP:(0):Returning Actual lifetime: 3600 032038: May 20 12:00:33.478 EDT: ISAKMP:(0)::Started lifetime timer: 3600. 032039: May 20 12:00:33.478 EDT: ISAKMP:(0): processing vendor id payload 032040: May 20 12:00:33.478 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch 032041: May 20 12:00:33.478 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947 032042: May 20 12:00:33.478 EDT: ISAKMP:(0): processing vendor id payload 032043: May 20 12:00:33.478 EDT: ISAKMP:(0): processing IKE frag vendor id payload 032044: May 20 12:00:33.478 EDT: ISAKMP:(0):Support for IKE Fragmentation not enabled 032045: May 20 12:00:33.478 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE 032046: May 20 12:00:33.478 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State = IKE_I_MM2 032047: May 20 12:00:33.478 EDT: ISAKMP:(0): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) MM_SA_SETUP 032048: May 20 12:00:33.478 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet. 032049: May 20 12:00:33.478 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE 032050: May 20 12:00:33.478 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State = IKE_I_MM3 032051: May 20 12:00:33.506 EDT: ISAKMP (0): received packet from 19.16.19.136 dport 500 sport 500 Global (I) MM_SA_SETUP 032052: May 20 12:00:33.506 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032053: May 20 12:00:33.506 EDT: ISAKMP:(0):Old State = IKE_I_MM3 New State = IKE_I_MM4 032054: May 20 12:00:33.510 EDT: ISAKMP:(0): processing KE payload. message ID = 0 032055: May 20 12:00:33.534 EDT: ISAKMP:(0): processing NONCE payload. message ID = 0 032056: May 20 12:00:33.534 EDT: ISAKMP:(0):found peer pre-shared key matching 19.16.19.136 032057: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload 032058: May 20 12:00:33.534 EDT: ISAKMP:(1112): vendor ID is Unity 032059: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload 032060: May 20 12:00:33.534 EDT: ISAKMP:(1112): vendor ID seems Unity/DPD but major 245 mismatch 032061: May 20 12:00:33.534 EDT: ISAKMP:(1112): vendor ID is XAUTH 032062: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload 032063: May 20 12:00:33.534 EDT: ISAKMP:(1112): speaking to another IOS box! 032064: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload 032065: May 20 12:00:33.534 EDT: ISAKMP:(1112):vendor ID seems Unity/DPD but hash mismatch 032066: May 20 12:00:33.534 EDT: ISAKMP:received payload type 20 032067: May 20 12:00:33.534 EDT: ISAKMP (1112): His hash no match - this node outside NAT 032068: May 20 12:00:33.534 EDT: ISAKMP:received payload type 20 032069: May 20 12:00:33.534 EDT: ISAKMP (1112): No NAT Found for self or peer 032070: May 20 12:00:33.534 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE 032071: May 20 12:00:33.534 EDT: ISAKMP:(1112):Old State = IKE_I_MM4 New State = IKE_I_MM4 032072: May 20 12:00:33.538 EDT: ISAKMP:(1112):Send initial contact 032073: May 20 12:00:33.538 EDT: ISAKMP:(1112):SA is doing pre-shared key authentication using id type ID_IPV4_ADDR 032074: May 20 12:00:33.538 EDT: ISAKMP (1112): ID payload next-payload : 8 type : 1 address : 19.24.11.142 protocol : 17 port : 500 length : 12 032075: May 20 12:00:33.538 EDT: ISAKMP:(1112):Total payload length: 12 032076: May 20 12:00:33.538 EDT: ISAKMP:(1112): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) MM_KEY_EXCH 032077: May 20 12:00:33.538 EDT: ISAKMP:(1112):Sending an IKE IPv4 Packet. 032078: May 20 12:00:33.538 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE 032079: May 20 12:00:33.538 EDT: ISAKMP:(1112):Old State = IKE_I_MM4 New State = IKE_I_MM5 032080: May 20 12:00:33.566 EDT: ISAKMP (1112): received packet from 19.16.19.136 dport 500 sport 500 Global (I) MM_KEY_EXCH 032081: May 20 12:00:33.566 EDT: ISAKMP:(1112): processing ID payload. message ID = 0 032082: May 20 12:00:33.566 EDT: ISAKMP (1112): ID payload next-payload : 8 type : 1 address : 19.16.19.136 protocol : 17 port : 0 length : 12 032083: May 20 12:00:33.566 EDT: ISAKMP:(0):: peer matches *none* of the profiles 032084: May 20 12:00:33.566 EDT: ISAKMP:(1112): processing HASH payload. message ID = 0 032085: May 20 12:00:33.566 EDT: ISAKMP:received payload type 17 032086: May 20 12:00:33.566 EDT: ISAKMP:(1112): processing vendor id payload 032087: May 20 12:00:33.566 EDT: ISAKMP:(1112): vendor ID is DPD 032088: May 20 12:00:33.566 EDT: ISAKMP:(1112):SA authentication status: authenticated 032089: May 20 12:00:33.566 EDT: ISAKMP:(1112):SA has been authenticated with 19.16.19.136 032090: May 20 12:00:33.566 EDT: ISAKMP: Trying to insert a peer 19.24.11.142/19.16.19.136/500/, and inserted successfully 313D5AA8. 032091: May 20 12:00:33.566 EDT: ISAKMP:(1112):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032092: May 20 12:00:33.566 EDT: ISAKMP:(1112):Old State = IKE_I_MM5 New State = IKE_I_MM6 032093: May 20 12:00:33.566 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE 032094: May 20 12:00:33.566 EDT: ISAKMP:(1112):Old State = IKE_I_MM6 New State = IKE_I_MM6 032095: May 20 12:00:33.566 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE 032096: May 20 12:00:33.566 EDT: ISAKMP:(1112):Old State = IKE_I_MM6 New State = IKE_P1_COMPLETE 032097: May 20 12:00:33.570 EDT: ISAKMP:(1112):beginning Quick Mode exchange, M-ID of 3822625957 032098: May 20 12:00:33.570 EDT: ISAKMP:(1112):QM Initiator gets spi 032099: May 20 12:00:33.570 EDT: ISAKMP:(1112): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE 032100: May 20 12:00:33.570 EDT: ISAKMP:(1112):Sending an IKE IPv4 Packet. 032101: May 20 12:00:33.570 EDT: ISAKMP:(1112):Node 3822625957, Input = IKE_MESG_INTERNAL, IKE_INIT_QM 032102: May 20 12:00:33.570 EDT: ISAKMP:(1112):Old State = IKE_QM_READY New State = IKE_QM_I_QM1 032103: May 20 12:00:33.570 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL, IKE_PHASE1_COMPLETE 032104: May 20 12:00:33.570 EDT: ISAKMP:(1112):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE 032105: May 20 12:00:33.602 EDT: ISAKMP (1112): received packet from 19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE 032106: May 20 12:00:33.602 EDT: ISAKMP: set new node 497356209 to QM_IDLE 032107: May 20 12:00:33.602 EDT: ISAKMP:(1112): processing HASH payload. message ID = 497356209 032108: May 20 12:00:33.602 EDT: ISAKMP:(1112): processing NOTIFY PROPOSAL_NOT_CHOSEN protocol 3 spi 0, message ID = 497356209, sa = 0x2A271B9C 032109: May 20 12:00:33.602 EDT: ISAKMP:(1112):deleting node 497356209 error FALSE reason "Informational (in) state 1" 032110: May 20 12:00:33.602 EDT: ISAKMP:(1112):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY 032111: May 20 12:00:33.602 EDT: ISAKMP:(1112):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE 032112: May 20 12:00:33.602 EDT: ISAKMP (1112): received packet from 19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE 032113: May 20 12:00:33.602 EDT: ISAKMP: set new node 309704327 to QM_IDLE 032114: May 20 12:00:33.602 EDT: ISAKMP:(1112): processing HASH payload. message ID = 309704327 032115: May 20 12:00:33.602 EDT: ISAKMP:received payload type 18 032116: May 20 12:00:33.602 EDT: ISAKMP:(1112):Processing delete with reason payload 032117: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete doi = 1 032118: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete protocol id = 1 032119: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete spi_size = 16 032120: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete num spis = 1 032121: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete_reason = 10 032122: May 20 12:00:33.606 EDT: ISAKMP:(1112): processing DELETE_WITH_REASON payload, message ID = 309704327, reason: Unknown delete reason! 032123: May 20 12:00:33.606 EDT: ISAKMP:(1112):peer does not do paranoid keepalives. 032124: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting SA reason "IKE SA Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136) 032125: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting node 309704327 error FALSE reason "Informational (in) state 1" 032126: May 20 12:00:33.606 EDT: ISAKMP: set new node -1825006387 to QM_IDLE 032127: May 20 12:00:33.606 EDT: ISAKMP:(1112): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE 032128: May 20 12:00:33.606 EDT: ISAKMP:(1112):Sending an IKE IPv4 Packet. 032129: May 20 12:00:33.606 EDT: ISAKMP:(1112):purging node -1825006387 032130: May 20 12:00:33.606 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL, IKE_PHASE1_DEL 032131: May 20 12:00:33.606 EDT: ISAKMP:(1112):Old State = IKE_P1_COMPLETE New State = IKE_DEST_SA 032132: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting SA reason "IKE SA Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136) 032133: May 20 12:00:33.606 EDT: ISAKMP: Unlocking peer struct 0x313D5AA8 for isadb_mark_sa_deleted(), count 0 032134: May 20 12:00:33.606 EDT: ISAKMP: Deleting peer node by peer_reap for 19.16.19.136: 313D5AA8 032135: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting node -472341339 error FALSE reason "IKE deleted" 032136: May 20 12:00:33.606 EDT: ISAKMP:(1112):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032137: May 20 12:00:33.606 EDT: ISAKMP:(1112):Old State = IKE_DEST_SA New State = IKE_DEST_SA R1-IPSEC1# 032138: May 20 12:00:33.606 EDT: IPSEC(key_engine): got a queue event with 1 KMI message(s) R1-IPSEC1# 032139: May 20 12:01:03.441 EDT: IPSEC(key_engine): request timer fired: count = 1, (identity) local= 19.24.11.142:0, remote= 19.16.19.136:0, local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1), remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1) 032140: May 20 12:01:03.441 EDT: IPSEC(sa_request): , (key eng. msg.) OUTBOUND local= 19.24.11.142:500, remote= 19.16.19.136:500, local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1), remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1), protocol= ESP, transform= esp-aes 256 esp-sha-hmac (Tunnel), lifedur= 3600s and 4608000kb, spi= 0x0(0), conn_id= 0, keysize= 256, flags= 0x0 032141: May 20 12:01:03.441 EDT: ISAKMP:(0): SA request profile is (NULL) 032142: May 20 12:01:03.441 EDT: ISAKMP: Created a peer struct for 19.16.19.136, peer port 500 032143: May 20 12:01:03.441 EDT: ISAKMP: New peer created peer = 0x313D3120 peer_handle = 0x8000004B 032144: May 20 12:01:03.441 EDT: ISAKMP: Locking peer struct 0x313D3120, refcount 1 for isakmp_initiator 032145: May 20 12:01:03.441 EDT: ISAKMP: local port 500, remote port 500 032146: May 20 12:01:03.441 EDT: ISAKMP: set new node 0 to QM_IDLE 032147: May 20 12:01:03.441 EDT: ISAKMP: Find a dup sa in the avl tree during calling isadb_insert sa = 30038454 032148: May 20 12:01:03.441 EDT: %CRYPTO-5-IKMP_AG_MODE_DISABLED: Unable to initiate or respond to Aggressive Mode while disabled 032149: May 20 12:01:03.441 EDT: ISAKMP:(0):Can not start Aggressive mode, trying Main mode. 032150: May 20 12:01:03.441 EDT: ISAKMP:(0):found peer pre-shared key matching 19.16.19.136 032151: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-rfc3947 ID 032152: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-07 ID 032153: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-03 ID 032154: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-02 ID 032155: May 20 12:01:03.441 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_IPSEC, IKE_SA_REQ_MM 032156: May 20 12:01:03.441 EDT: ISAKMP:(0):Old State = IKE_READY New State = IKE_I_MM1 032157: May 20 12:01:03.441 EDT: ISAKMP:(0): beginning Main Mode exchange 032158: May 20 12:01:03.441 EDT: ISAKMP:(0): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) MM_NO_STATE 032159: May 20 12:01:03.441 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet. 032160: May 20 12:01:03.469 EDT: ISAKMP (0): received packet from 19.16.19.136 dport 500 sport 500 Global (I) MM_NO_STATE 032161: May 20 12:01:03.469 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032162: May 20 12:01:03.469 EDT: ISAKMP:(0):Old State = IKE_I_MM1 New State = IKE_I_MM2 032163: May 20 12:01:03.469 EDT: ISAKMP:(0): processing SA payload. message ID = 0 032164: May 20 12:01:03.469 EDT: ISAKMP:(0): processing vendor id payload 032165: May 20 12:01:03.469 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch 032166: May 20 12:01:03.469 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947 032167: May 20 12:01:03.469 EDT: ISAKMP:(0): processing vendor id payload 032168: May 20 12:01:03.473 EDT: ISAKMP:(0): processing IKE frag vendor id payload 032169: May 20 12:01:03.473 EDT: ISAKMP:(0):Support for IKE Fragmentation not enabled 032170: May 20 12:01:03.473 EDT: ISAKMP:(0):found peer pre-shared key matching 19.16.19.136 032171: May 20 12:01:03.473 EDT: ISAKMP:(0): local preshared key found 032172: May 20 12:01:03.473 EDT: ISAKMP : Scanning profiles for xauth ... 032173: May 20 12:01:03.473 EDT: ISAKMP:(0):Checking ISAKMP transform 1 against priority 1 policy 032174: May 20 12:01:03.473 EDT: ISAKMP: encryption 3DES-CBC 032175: May 20 12:01:03.473 EDT: ISAKMP: hash SHA 032176: May 20 12:01:03.473 EDT: ISAKMP: default group 2 032177: May 20 12:01:03.473 EDT: ISAKMP: auth pre-share 032178: May 20 12:01:03.473 EDT: ISAKMP: life type in seconds 032179: May 20 12:01:03.473 EDT: ISAKMP: life duration (basic) of 3600 032180: May 20 12:01:03.473 EDT: ISAKMP:(0):atts are acceptable. Next payload is 0 032181: May 20 12:01:03.473 EDT: ISAKMP:(0):Acceptable atts:actual life: 0 032182: May 20 12:01:03.473 EDT: ISAKMP:(0):Acceptable atts:life: 0 032183: May 20 12:01:03.473 EDT: ISAKMP:(0):Basic life_in_seconds:3600 032184: May 20 12:01:03.473 EDT: ISAKMP:(0):Returning Actual lifetime: 3600 032185: May 20 12:01:03.473 EDT: ISAKMP:(0)::Started lifetime timer: 3600. 032186: May 20 12:01:03.473 EDT: ISAKMP:(0): processing vendor id payload 032187: May 20 12:01:03.473 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but major 69 mismatch 032188: May 20 12:01:03.473 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947 032189: May 20 12:01:03.473 EDT: ISAKMP:(0): processing vendor id payload 032190: May 20 12:01:03.473 EDT: ISAKMP:(0): processing IKE frag vendor id payload 032191: May 20 12:01:03.473 EDT: ISAKMP:(0):Support for IKE Fragmentation not enabled 032192: May 20 12:01:03.473 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE 032193: May 20 12:01:03.473 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State = IKE_I_MM2 032194: May 20 12:01:03.473 EDT: ISAKMP:(0): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) MM_SA_SETUP 032195: May 20 12:01:03.473 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet. 032196: May 20 12:01:03.473 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE 032197: May 20 12:01:03.473 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State = IKE_I_MM3 032198: May 20 12:01:03.501 EDT: ISAKMP (0): received packet from 19.16.19.136 dport 500 sport 500 Global (I) MM_SA_SETUP 032199: May 20 12:01:03.505 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032200: May 20 12:01:03.505 EDT: ISAKMP:(0):Old State = IKE_I_MM3 New State = IKE_I_MM4 032201: May 20 12:01:03.505 EDT: ISAKMP:(0): processing KE payload. message ID = 0 032202: May 20 12:01:03.529 EDT: ISAKMP:(0): processing NONCE payload. message ID = 0 032203: May 20 12:01:03.529 EDT: ISAKMP:(0):found peer pre-shared key matching 19.16.19.136 032204: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload 032205: May 20 12:01:03.529 EDT: ISAKMP:(1113): vendor ID is Unity 032206: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload 032207: May 20 12:01:03.529 EDT: ISAKMP:(1113): vendor ID seems Unity/DPD but major 9 mismatch 032208: May 20 12:01:03.529 EDT: ISAKMP:(1113): vendor ID is XAUTH 032209: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload 032210: May 20 12:01:03.529 EDT: ISAKMP:(1113): speaking to another IOS box! 032211: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload 032212: May 20 12:01:03.529 EDT: ISAKMP:(1113):vendor ID seems Unity/DPD but hash mismatch 032213: May 20 12:01:03.529 EDT: ISAKMP:received payload type 20 032214: May 20 12:01:03.529 EDT: ISAKMP (1113): His hash no match - this node outside NAT 032215: May 20 12:01:03.529 EDT: ISAKMP:received payload type 20 032216: May 20 12:01:03.529 EDT: ISAKMP (1113): No NAT Found for self or peer 032217: May 20 12:01:03.529 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE 032218: May 20 12:01:03.529 EDT: ISAKMP:(1113):Old State = IKE_I_MM4 New State = IKE_I_MM4 032219: May 20 12:01:03.533 EDT: ISAKMP:(1113):Send initial contact 032220: May 20 12:01:03.533 EDT: ISAKMP:(1113):SA is doing pre-shared key authentication using id type ID_IPV4_ADDR 032221: May 20 12:01:03.533 EDT: ISAKMP (1113): ID payload next-payload : 8 type : 1 address : 19.24.11.142 protocol : 17 port : 500 length : 12 032222: May 20 12:01:03.533 EDT: ISAKMP:(1113):Total payload length: 12 032223: May 20 12:01:03.533 EDT: ISAKMP:(1113): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) MM_KEY_EXCH 032224: May 20 12:01:03.533 EDT: ISAKMP:(1113):Sending an IKE IPv4 Packet. 032225: May 20 12:01:03.533 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE 032226: May 20 12:01:03.533 EDT: ISAKMP:(1113):Old State = IKE_I_MM4 New State = IKE_I_MM5 032227: May 20 12:01:03.561 EDT: ISAKMP (1113): received packet from 19.16.19.136 dport 500 sport 500 Global (I) MM_KEY_EXCH 032228: May 20 12:01:03.561 EDT: ISAKMP:(1113): processing ID payload. message ID = 0 032229: May 20 12:01:03.561 EDT: ISAKMP (1113): ID payload next-payload : 8 type : 1 address : 19.16.19.136 protocol : 17 port : 0 length : 12 032230: May 20 12:01:03.561 EDT: ISAKMP:(0):: peer matches *none* of the profiles 032231: May 20 12:01:03.561 EDT: ISAKMP:(1113): processing HASH payload. message ID = 0 032232: May 20 12:01:03.561 EDT: ISAKMP:received payload type 17 032233: May 20 12:01:03.561 EDT: ISAKMP:(1113): processing vendor id payload 032234: May 20 12:01:03.561 EDT: ISAKMP:(1113): vendor ID is DPD 032235: May 20 12:01:03.561 EDT: ISAKMP:(1113):SA authentication status: authenticated 032236: May 20 12:01:03.561 EDT: ISAKMP:(1113):SA has been authenticated with 19.16.19.136 032237: May 20 12:01:03.561 EDT: ISAKMP: Trying to insert a peer 19.24.11.142/19.16.19.136/500/, and inserted successfully 313D3120. 032238: May 20 12:01:03.561 EDT: ISAKMP:(1113):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032239: May 20 12:01:03.561 EDT: ISAKMP:(1113):Old State = IKE_I_MM5 New State = IKE_I_MM6 032240: May 20 12:01:03.561 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL, IKE_PROCESS_MAIN_MODE 032241: May 20 12:01:03.561 EDT: ISAKMP:(1113):Old State = IKE_I_MM6 New State = IKE_I_MM6 032242: May 20 12:01:03.561 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL, IKE_PROCESS_COMPLETE 032243: May 20 12:01:03.561 EDT: ISAKMP:(1113):Old State = IKE_I_MM6 New State = IKE_P1_COMPLETE 032244: May 20 12:01:03.561 EDT: ISAKMP:(1113):beginning Quick Mode exchange, M-ID of 2581849008 032245: May 20 12:01:03.565 EDT: ISAKMP:(1113):QM Initiator gets spi 032246: May 20 12:01:03.565 EDT: ISAKMP:(1113): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE 032247: May 20 12:01:03.565 EDT: ISAKMP:(1113):Sending an IKE IPv4 Packet. 032248: May 20 12:01:03.565 EDT: ISAKMP:(1113):Node 2581849008, Input = IKE_MESG_INTERNAL, IKE_INIT_QM 032249: May 20 12:01:03.565 EDT: ISAKMP:(1113):Old State = IKE_QM_READY New State = IKE_QM_I_QM1 032250: May 20 12:01:03.565 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL, IKE_PHASE1_COMPLETE 032251: May 20 12:01:03.565 EDT: ISAKMP:(1113):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE 032252: May 20 12:01:03.597 EDT: ISAKMP (1113): received packet from 19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE 032253: May 20 12:01:03.597 EDT: ISAKMP: set new node 1341887425 to QM_IDLE 032254: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing HASH payload. message ID = 1341887425 032255: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing NOTIFY PROPOSAL_NOT_CHOSEN protocol 3 spi 0, message ID = 1341887425, sa = 0x30038454 032256: May 20 12:01:03.597 EDT: ISAKMP:(1113):deleting node 1341887425 error FALSE reason "Informational (in) state 1" 032257: May 20 12:01:03.597 EDT: ISAKMP:(1113):Input = IKE_MESG_FROM_PEER, IKE_INFO_NOTIFY 032258: May 20 12:01:03.597 EDT: ISAKMP:(1113):Old State = IKE_P1_COMPLETE New State = IKE_P1_COMPLETE 032259: May 20 12:01:03.597 EDT: ISAKMP (1113): received packet from 19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE 032260: May 20 12:01:03.597 EDT: ISAKMP: set new node 1837926342 to QM_IDLE 032261: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing HASH payload. message ID = 1837926342 032262: May 20 12:01:03.597 EDT: ISAKMP:received payload type 18 032263: May 20 12:01:03.597 EDT: ISAKMP:(1113):Processing delete with reason payload 032264: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete doi = 1 032265: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete protocol id = 1 032266: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete spi_size = 16 032267: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete num spis = 1 032268: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete_reason = 10 032269: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing DELETE_WITH_REASON payload, message ID = 1837926342, reason: Unknown delete reason! 032270: May 20 12:01:03.597 EDT: ISAKMP:(1113):peer does not do paranoid keepalives. 032271: May 20 12:01:03.597 EDT: ISAKMP:(1113):deleting SA reason "IKE SA Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136) 032272: May 20 12:01:03.597 EDT: ISAKMP:(1113):deleting node 1837926342 error FALSE reason "Informational (in) state 1" 032273: May 20 12:01:03.601 EDT: ISAKMP: set new node -577632662 to QM_IDLE 032274: May 20 12:01:03.601 EDT: ISAKMP:(1113): sending packet to 19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE 032275: May 20 12:01:03.601 EDT: ISAKMP:(1113):Sending an IKE IPv4 Packet. 032276: May 20 12:01:03.601 EDT: ISAKMP:(1113):purging node -577632662 032277: May 20 12:01:03.601 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL, IKE_PHASE1_DEL 032278: May 20 12:01:03.601 EDT: ISAKMP:(1113):Old State = IKE_P1_COMPLETE New State = IKE_DEST_SA 032279: May 20 12:01:03.601 EDT: ISAKMP:(1113):deleting SA reason "IKE SA Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136) 032280: May 20 12:01:03.601 EDT: ISAKMP: Unlocking peer struct 0x313D3120 for isadb_mark_sa_deleted(), count 0 032281: May 20 12:01:03.601 EDT: ISAKMP: Deleting peer node by peer_reap for 19.16.19.136: 313D3120 032282: May 20 12:01:03.601 EDT: ISAKMP:(1113):deleting node -1713118288 error FALSE reason "IKE deleted" 032283: May 20 12:01:03.601 EDT: ISAKMP:(1113):Input = IKE_MESG_FROM_PEER, IKE_MM_EXCH 032284: May 20 12:01:03.601 EDT: ISAKMP:(1113):Old State = IKE_DEST_SA New State = IKE_DEST_SA R1-IPSEC1# 032285: May 20 12:01:03.601 EDT: IPSEC(key_engine): got a queue event with 1 KMI message(s) R1-IPSEC1# 032286: May 20 12:01:23.601 EDT: ISAKMP:(1112):purging node 497356209 032287: May 20 12:01:23.605 EDT: ISAKMP:(1112):purging node 309704327 032288: May 20 12:01:23.605 EDT: ISAKMP:(1112):purging node -472341339 R1-IPSEC1# 032289: May 20 12:01:33.441 EDT: IPSEC(key_engine): request timer fired: count = 2, (identity) local= 19.24.11.142:0, remote= 19.16.19.136:0, local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1), remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1) 032290: May 20 12:01:33.605 EDT: ISAKMP:(1112):purging SA., sa=2A271B9C, delme=2A271B9C R1-IPSEC1# 032291: May 20 12:01:53.597 EDT: ISAKMP:(1113):purging node 1341887425 032292: May 20 12:01:53.597 EDT: ISAKMP:(1113):purging node 1837926342 032293: May 20 12:01:53.601 EDT: ISAKMP:(1113):purging node -1713118288 R1-IPSEC1# 032294: May 20 12:02:03.601 EDT: ISAKMP:(1113):purging SA., sa=30038454, delme=30038454 R1-IPSEC1# 032295: May 20 12:02:21.009 EDT: %SEC-6-IPACCESSLOGP: list 101 permitted tcp 19.24.11.9(47889) -> 0.0.0.0(22), 1 packet R1-IPSEC1#
R1-IPSEC1#
031993: May 20 12:00:33.442 EDT: IPSEC(sa_request): ,
(key eng. msg.) OUTBOUND local= 19.24.11.142:500, remote=
19.16.19.136:500,
local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1),
remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1),
protocol= ESP, transform= esp-aes 256 esp-sha-hmac (Tunnel),
lifedur= 3600s and 4608000kb,
spi= 0x0(0), conn_id= 0, keysize= 256, flags= 0x0
031994: May 20 12:00:33.442 EDT: ISAKMP:(0): SA request profile is (NULL)
031995: May 20 12:00:33.442 EDT: ISAKMP: Created a peer struct for
19.16.19.136, peer port 500
031996: May 20 12:00:33.442 EDT: ISAKMP: New peer created peer = 0x313D5AA8
peer_handle = 0x80000049
031997: May 20 12:00:33.442 EDT: ISAKMP: Locking peer struct 0x313D5AA8,
refcount 1 for isakmp_initiator
031998: May 20 12:00:33.446 EDT: ISAKMP: local port 500, remote port 500
031999: May 20 12:00:33.446 EDT: ISAKMP: set new node 0 to QM_IDLE
032000: May 20 12:00:33.446 EDT: ISAKMP:(0):insert sa successfully sa =
2A271B9C
032001: May 20 12:00:33.446 EDT: %CRYPTO-5-IKMP_AG_MODE_DISABLED: Unable to
initiate or respond to Aggressive Mode while disabled
032002: May 20 12:00:33.446 EDT: ISAKMP:(0):Can not start Aggressive mode,
trying Main mode.
032003: May 20 12:00:33.446 EDT: ISAKMP:(0):found peer pre-shared key matching
19.16.19.136
032004: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-rfc3947
ID
032005: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-07 ID
032006: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-03 ID
032007: May 20 12:00:33.446 EDT: ISAKMP:(0): constructed NAT-T vendor-02 ID
032008: May 20 12:00:33.446 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_IPSEC,
IKE_SA_REQ_MM
032009: May 20 12:00:33.446 EDT: ISAKMP:(0):Old State = IKE_READY New State =
IKE_I_MM1
032010: May 20 12:00:33.446 EDT: ISAKMP:(0): beginning Main Mode exchange
032011: May 20 12:00:33.446 EDT: ISAKMP:(0): sending packet to 19.16.19.136
my_port 500 peer_port 500 (I) MM_NO_STATE
032012: May 20 12:00:33.446 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet.
032013: May 20 12:00:33.474 EDT: ISAKMP (0): received packet from
19.16.19.136 dport 500 sport 500 Global (I) MM_NO_STATE
032014: May 20 12:00:33.474 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032015: May 20 12:00:33.474 EDT: ISAKMP:(0):Old State = IKE_I_MM1 New State =
IKE_I_MM2
032016: May 20 12:00:33.474 EDT: ISAKMP:(0): processing SA payload. message ID
= 0
032017: May 20 12:00:33.474 EDT: ISAKMP:(0): processing vendor id payload
032018: May 20 12:00:33.474 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but
major 69 mismatch
032019: May 20 12:00:33.474 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947
032020: May 20 12:00:33.474 EDT: ISAKMP:(0): processing vendor id payload
032021: May 20 12:00:33.474 EDT: ISAKMP:(0): processing IKE frag vendor id
payload
032022: May 20 12:00:33.474 EDT: ISAKMP:(0):Support for IKE Fragmentation not
enabled
032023: May 20 12:00:33.474 EDT: ISAKMP:(0):found peer pre-shared key matching
19.16.19.136
032024: May 20 12:00:33.478 EDT: ISAKMP:(0): local preshared key found
032025: May 20 12:00:33.478 EDT: ISAKMP : Scanning profiles for xauth ...
032026: May 20 12:00:33.478 EDT: ISAKMP:(0):Checking ISAKMP transform 1
against priority 1 policy
032027: May 20 12:00:33.478 EDT: ISAKMP: encryption 3DES-CBC
032028: May 20 12:00:33.478 EDT: ISAKMP: hash SHA
032029: May 20 12:00:33.478 EDT: ISAKMP: default group 2
032030: May 20 12:00:33.478 EDT: ISAKMP: auth pre-share
032031: May 20 12:00:33.478 EDT: ISAKMP: life type in seconds
032032: May 20 12:00:33.478 EDT: ISAKMP: life duration (basic) of 3600
032033: May 20 12:00:33.478 EDT: ISAKMP:(0):atts are acceptable. Next payload
is 0
032034: May 20 12:00:33.478 EDT: ISAKMP:(0):Acceptable atts:actual life: 0
032035: May 20 12:00:33.478 EDT: ISAKMP:(0):Acceptable atts:life: 0
032036: May 20 12:00:33.478 EDT: ISAKMP:(0):Basic life_in_seconds:3600
032037: May 20 12:00:33.478 EDT: ISAKMP:(0):Returning Actual lifetime: 3600
032038: May 20 12:00:33.478 EDT: ISAKMP:(0)::Started lifetime timer: 3600.
032039: May 20 12:00:33.478 EDT: ISAKMP:(0): processing vendor id payload
032040: May 20 12:00:33.478 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but
major 69 mismatch
032041: May 20 12:00:33.478 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947
032042: May 20 12:00:33.478 EDT: ISAKMP:(0): processing vendor id payload
032043: May 20 12:00:33.478 EDT: ISAKMP:(0): processing IKE frag vendor id
payload
032044: May 20 12:00:33.478 EDT: ISAKMP:(0):Support for IKE Fragmentation not
enabled
032045: May 20 12:00:33.478 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_MAIN_MODE
032046: May 20 12:00:33.478 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State =
IKE_I_MM2
032047: May 20 12:00:33.478 EDT: ISAKMP:(0): sending packet to 19.16.19.136
my_port 500 peer_port 500 (I) MM_SA_SETUP
032048: May 20 12:00:33.478 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet.
032049: May 20 12:00:33.478 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_COMPLETE
032050: May 20 12:00:33.478 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State =
IKE_I_MM3
032051: May 20 12:00:33.506 EDT: ISAKMP (0): received packet from
19.16.19.136 dport 500 sport 500 Global (I) MM_SA_SETUP
032052: May 20 12:00:33.506 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032053: May 20 12:00:33.506 EDT: ISAKMP:(0):Old State = IKE_I_MM3 New State =
IKE_I_MM4
032054: May 20 12:00:33.510 EDT: ISAKMP:(0): processing KE payload. message ID
= 0
032055: May 20 12:00:33.534 EDT: ISAKMP:(0): processing NONCE payload. message
ID = 0
032056: May 20 12:00:33.534 EDT: ISAKMP:(0):found peer pre-shared key matching
19.16.19.136
032057: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload
032058: May 20 12:00:33.534 EDT: ISAKMP:(1112): vendor ID is Unity
032059: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload
032060: May 20 12:00:33.534 EDT: ISAKMP:(1112): vendor ID seems Unity/DPD but
major 245 mismatch
032061: May 20 12:00:33.534 EDT: ISAKMP:(1112): vendor ID is XAUTH
032062: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload
032063: May 20 12:00:33.534 EDT: ISAKMP:(1112): speaking to another IOS box!
032064: May 20 12:00:33.534 EDT: ISAKMP:(1112): processing vendor id payload
032065: May 20 12:00:33.534 EDT: ISAKMP:(1112):vendor ID seems Unity/DPD but
hash mismatch
032066: May 20 12:00:33.534 EDT: ISAKMP:received payload type 20
032067: May 20 12:00:33.534 EDT: ISAKMP (1112): His hash no match - this node
outside NAT
032068: May 20 12:00:33.534 EDT: ISAKMP:received payload type 20
032069: May 20 12:00:33.534 EDT: ISAKMP (1112): No NAT Found for self or peer
032070: May 20 12:00:33.534 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_MAIN_MODE
032071: May 20 12:00:33.534 EDT: ISAKMP:(1112):Old State = IKE_I_MM4 New
State = IKE_I_MM4
032072: May 20 12:00:33.538 EDT: ISAKMP:(1112):Send initial contact
032073: May 20 12:00:33.538 EDT: ISAKMP:(1112):SA is doing pre-shared key
authentication using id type ID_IPV4_ADDR
032074: May 20 12:00:33.538 EDT: ISAKMP (1112): ID payload
next-payload : 8
type : 1
address : 19.24.11.142
protocol : 17
port : 500
length : 12
032075: May 20 12:00:33.538 EDT: ISAKMP:(1112):Total payload length: 12
032076: May 20 12:00:33.538 EDT: ISAKMP:(1112): sending packet to
19.16.19.136 my_port 500 peer_port 500 (I) MM_KEY_EXCH
032077: May 20 12:00:33.538 EDT: ISAKMP:(1112):Sending an IKE IPv4 Packet.
032078: May 20 12:00:33.538 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_COMPLETE
032079: May 20 12:00:33.538 EDT: ISAKMP:(1112):Old State = IKE_I_MM4 New
State = IKE_I_MM5
032080: May 20 12:00:33.566 EDT: ISAKMP (1112): received packet from
19.16.19.136 dport 500 sport 500 Global (I) MM_KEY_EXCH
032081: May 20 12:00:33.566 EDT: ISAKMP:(1112): processing ID payload. message
ID = 0
032082: May 20 12:00:33.566 EDT: ISAKMP (1112): ID payload
next-payload : 8
type : 1
address : 19.16.19.136
protocol : 17
port : 0
length : 12
032083: May 20 12:00:33.566 EDT: ISAKMP:(0):: peer matches *none* of the
profiles
032084: May 20 12:00:33.566 EDT: ISAKMP:(1112): processing HASH payload.
message ID = 0
032085: May 20 12:00:33.566 EDT: ISAKMP:received payload type 17
032086: May 20 12:00:33.566 EDT: ISAKMP:(1112): processing vendor id payload
032087: May 20 12:00:33.566 EDT: ISAKMP:(1112): vendor ID is DPD
032088: May 20 12:00:33.566 EDT: ISAKMP:(1112):SA authentication status:
authenticated
032089: May 20 12:00:33.566 EDT: ISAKMP:(1112):SA has been authenticated with
19.16.19.136
032090: May 20 12:00:33.566 EDT: ISAKMP: Trying to insert a peer
19.24.11.142/19.16.19.136/500/, and inserted successfully 313D5AA8.
032091: May 20 12:00:33.566 EDT: ISAKMP:(1112):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032092: May 20 12:00:33.566 EDT: ISAKMP:(1112):Old State = IKE_I_MM5 New
State = IKE_I_MM6
032093: May 20 12:00:33.566 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_MAIN_MODE
032094: May 20 12:00:33.566 EDT: ISAKMP:(1112):Old State = IKE_I_MM6 New
State = IKE_I_MM6
032095: May 20 12:00:33.566 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_COMPLETE
032096: May 20 12:00:33.566 EDT: ISAKMP:(1112):Old State = IKE_I_MM6 New
State = IKE_P1_COMPLETE
032097: May 20 12:00:33.570 EDT: ISAKMP:(1112):beginning Quick Mode exchange,
M-ID of 3822625957
032098: May 20 12:00:33.570 EDT: ISAKMP:(1112):QM Initiator gets spi
032099: May 20 12:00:33.570 EDT: ISAKMP:(1112): sending packet to
19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE
032100: May 20 12:00:33.570 EDT: ISAKMP:(1112):Sending an IKE IPv4 Packet.
032101: May 20 12:00:33.570 EDT: ISAKMP:(1112):Node 3822625957, Input =
IKE_MESG_INTERNAL, IKE_INIT_QM
032102: May 20 12:00:33.570 EDT: ISAKMP:(1112):Old State = IKE_QM_READY New
State = IKE_QM_I_QM1
032103: May 20 12:00:33.570 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL,
IKE_PHASE1_COMPLETE
032104: May 20 12:00:33.570 EDT: ISAKMP:(1112):Old State = IKE_P1_COMPLETE
New State = IKE_P1_COMPLETE
032105: May 20 12:00:33.602 EDT: ISAKMP (1112): received packet from
19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE
032106: May 20 12:00:33.602 EDT: ISAKMP: set new node 497356209 to QM_IDLE
032107: May 20 12:00:33.602 EDT: ISAKMP:(1112): processing HASH payload.
message ID = 497356209
032108: May 20 12:00:33.602 EDT: ISAKMP:(1112): processing NOTIFY
PROPOSAL_NOT_CHOSEN protocol 3
spi 0, message ID = 497356209, sa = 0x2A271B9C
032109: May 20 12:00:33.602 EDT: ISAKMP:(1112):deleting node 497356209 error
FALSE reason "Informational (in) state 1"
032110: May 20 12:00:33.602 EDT: ISAKMP:(1112):Input = IKE_MESG_FROM_PEER,
IKE_INFO_NOTIFY
032111: May 20 12:00:33.602 EDT: ISAKMP:(1112):Old State = IKE_P1_COMPLETE
New State = IKE_P1_COMPLETE
032112: May 20 12:00:33.602 EDT: ISAKMP (1112): received packet from
19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE
032113: May 20 12:00:33.602 EDT: ISAKMP: set new node 309704327 to QM_IDLE
032114: May 20 12:00:33.602 EDT: ISAKMP:(1112): processing HASH payload.
message ID = 309704327
032115: May 20 12:00:33.602 EDT: ISAKMP:received payload type 18
032116: May 20 12:00:33.602 EDT: ISAKMP:(1112):Processing delete with reason
payload
032117: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete doi = 1
032118: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete protocol id = 1
032119: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete spi_size = 16
032120: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete num spis = 1
032121: May 20 12:00:33.602 EDT: ISAKMP:(1112):delete_reason = 10
032122: May 20 12:00:33.606 EDT: ISAKMP:(1112): processing DELETE_WITH_REASON
payload, message ID = 309704327, reason: Unknown delete reason!
032123: May 20 12:00:33.606 EDT: ISAKMP:(1112):peer does not do paranoid
keepalives.
032124: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting SA reason "IKE SA
Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136)
032125: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting node 309704327 error
FALSE reason "Informational (in) state 1"
032126: May 20 12:00:33.606 EDT: ISAKMP: set new node -1825006387 to QM_IDLE
032127: May 20 12:00:33.606 EDT: ISAKMP:(1112): sending packet to
19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE
032128: May 20 12:00:33.606 EDT: ISAKMP:(1112):Sending an IKE IPv4 Packet.
032129: May 20 12:00:33.606 EDT: ISAKMP:(1112):purging node -1825006387
032130: May 20 12:00:33.606 EDT: ISAKMP:(1112):Input = IKE_MESG_INTERNAL,
IKE_PHASE1_DEL
032131: May 20 12:00:33.606 EDT: ISAKMP:(1112):Old State = IKE_P1_COMPLETE
New State = IKE_DEST_SA
032132: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting SA reason "IKE SA
Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136)
032133: May 20 12:00:33.606 EDT: ISAKMP: Unlocking peer struct 0x313D5AA8 for
isadb_mark_sa_deleted(), count 0
032134: May 20 12:00:33.606 EDT: ISAKMP: Deleting peer node by peer_reap for
19.16.19.136: 313D5AA8
032135: May 20 12:00:33.606 EDT: ISAKMP:(1112):deleting node -472341339 error
FALSE reason "IKE deleted"
032136: May 20 12:00:33.606 EDT: ISAKMP:(1112):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032137: May 20 12:00:33.606 EDT: ISAKMP:(1112):Old State = IKE_DEST_SA New
State = IKE_DEST_SA
R1-IPSEC1#
032138: May 20 12:00:33.606 EDT: IPSEC(key_engine): got a queue event with 1
KMI message(s)
R1-IPSEC1#
032139: May 20 12:01:03.441 EDT: IPSEC(key_engine): request timer fired: count
= 1,
(identity) local= 19.24.11.142:0, remote= 19.16.19.136:0,
local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1),
remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1)
032140: May 20 12:01:03.441 EDT: IPSEC(sa_request): ,
(key eng. msg.) OUTBOUND local= 19.24.11.142:500, remote=
19.16.19.136:500,
local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1),
remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1),
protocol= ESP, transform= esp-aes 256 esp-sha-hmac (Tunnel),
lifedur= 3600s and 4608000kb,
spi= 0x0(0), conn_id= 0, keysize= 256, flags= 0x0
032141: May 20 12:01:03.441 EDT: ISAKMP:(0): SA request profile is (NULL)
032142: May 20 12:01:03.441 EDT: ISAKMP: Created a peer struct for
19.16.19.136, peer port 500
032143: May 20 12:01:03.441 EDT: ISAKMP: New peer created peer = 0x313D3120
peer_handle = 0x8000004B
032144: May 20 12:01:03.441 EDT: ISAKMP: Locking peer struct 0x313D3120,
refcount 1 for isakmp_initiator
032145: May 20 12:01:03.441 EDT: ISAKMP: local port 500, remote port 500
032146: May 20 12:01:03.441 EDT: ISAKMP: set new node 0 to QM_IDLE
032147: May 20 12:01:03.441 EDT: ISAKMP: Find a dup sa in the avl tree during
calling isadb_insert sa = 30038454
032148: May 20 12:01:03.441 EDT: %CRYPTO-5-IKMP_AG_MODE_DISABLED: Unable to
initiate or respond to Aggressive Mode while disabled
032149: May 20 12:01:03.441 EDT: ISAKMP:(0):Can not start Aggressive mode,
trying Main mode.
032150: May 20 12:01:03.441 EDT: ISAKMP:(0):found peer pre-shared key matching
19.16.19.136
032151: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-rfc3947
ID
032152: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-07 ID
032153: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-03 ID
032154: May 20 12:01:03.441 EDT: ISAKMP:(0): constructed NAT-T vendor-02 ID
032155: May 20 12:01:03.441 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_IPSEC,
IKE_SA_REQ_MM
032156: May 20 12:01:03.441 EDT: ISAKMP:(0):Old State = IKE_READY New State =
IKE_I_MM1
032157: May 20 12:01:03.441 EDT: ISAKMP:(0): beginning Main Mode exchange
032158: May 20 12:01:03.441 EDT: ISAKMP:(0): sending packet to 19.16.19.136
my_port 500 peer_port 500 (I) MM_NO_STATE
032159: May 20 12:01:03.441 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet.
032160: May 20 12:01:03.469 EDT: ISAKMP (0): received packet from
19.16.19.136 dport 500 sport 500 Global (I) MM_NO_STATE
032161: May 20 12:01:03.469 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032162: May 20 12:01:03.469 EDT: ISAKMP:(0):Old State = IKE_I_MM1 New State =
IKE_I_MM2
032163: May 20 12:01:03.469 EDT: ISAKMP:(0): processing SA payload. message ID
= 0
032164: May 20 12:01:03.469 EDT: ISAKMP:(0): processing vendor id payload
032165: May 20 12:01:03.469 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but
major 69 mismatch
032166: May 20 12:01:03.469 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947
032167: May 20 12:01:03.469 EDT: ISAKMP:(0): processing vendor id payload
032168: May 20 12:01:03.473 EDT: ISAKMP:(0): processing IKE frag vendor id
payload
032169: May 20 12:01:03.473 EDT: ISAKMP:(0):Support for IKE Fragmentation not
enabled
032170: May 20 12:01:03.473 EDT: ISAKMP:(0):found peer pre-shared key matching
19.16.19.136
032171: May 20 12:01:03.473 EDT: ISAKMP:(0): local preshared key found
032172: May 20 12:01:03.473 EDT: ISAKMP : Scanning profiles for xauth ...
032173: May 20 12:01:03.473 EDT: ISAKMP:(0):Checking ISAKMP transform 1
against priority 1 policy
032174: May 20 12:01:03.473 EDT: ISAKMP: encryption 3DES-CBC
032175: May 20 12:01:03.473 EDT: ISAKMP: hash SHA
032176: May 20 12:01:03.473 EDT: ISAKMP: default group 2
032177: May 20 12:01:03.473 EDT: ISAKMP: auth pre-share
032178: May 20 12:01:03.473 EDT: ISAKMP: life type in seconds
032179: May 20 12:01:03.473 EDT: ISAKMP: life duration (basic) of 3600
032180: May 20 12:01:03.473 EDT: ISAKMP:(0):atts are acceptable. Next payload
is 0
032181: May 20 12:01:03.473 EDT: ISAKMP:(0):Acceptable atts:actual life: 0
032182: May 20 12:01:03.473 EDT: ISAKMP:(0):Acceptable atts:life: 0
032183: May 20 12:01:03.473 EDT: ISAKMP:(0):Basic life_in_seconds:3600
032184: May 20 12:01:03.473 EDT: ISAKMP:(0):Returning Actual lifetime: 3600
032185: May 20 12:01:03.473 EDT: ISAKMP:(0)::Started lifetime timer: 3600.
032186: May 20 12:01:03.473 EDT: ISAKMP:(0): processing vendor id payload
032187: May 20 12:01:03.473 EDT: ISAKMP:(0): vendor ID seems Unity/DPD but
major 69 mismatch
032188: May 20 12:01:03.473 EDT: ISAKMP (0): vendor ID is NAT-T RFC 3947
032189: May 20 12:01:03.473 EDT: ISAKMP:(0): processing vendor id payload
032190: May 20 12:01:03.473 EDT: ISAKMP:(0): processing IKE frag vendor id
payload
032191: May 20 12:01:03.473 EDT: ISAKMP:(0):Support for IKE Fragmentation not
enabled
032192: May 20 12:01:03.473 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_MAIN_MODE
032193: May 20 12:01:03.473 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State =
IKE_I_MM2
032194: May 20 12:01:03.473 EDT: ISAKMP:(0): sending packet to 19.16.19.136
my_port 500 peer_port 500 (I) MM_SA_SETUP
032195: May 20 12:01:03.473 EDT: ISAKMP:(0):Sending an IKE IPv4 Packet.
032196: May 20 12:01:03.473 EDT: ISAKMP:(0):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_COMPLETE
032197: May 20 12:01:03.473 EDT: ISAKMP:(0):Old State = IKE_I_MM2 New State =
IKE_I_MM3
032198: May 20 12:01:03.501 EDT: ISAKMP (0): received packet from
19.16.19.136 dport 500 sport 500 Global (I) MM_SA_SETUP
032199: May 20 12:01:03.505 EDT: ISAKMP:(0):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032200: May 20 12:01:03.505 EDT: ISAKMP:(0):Old State = IKE_I_MM3 New State =
IKE_I_MM4
032201: May 20 12:01:03.505 EDT: ISAKMP:(0): processing KE payload. message ID
= 0
032202: May 20 12:01:03.529 EDT: ISAKMP:(0): processing NONCE payload. message
ID = 0
032203: May 20 12:01:03.529 EDT: ISAKMP:(0):found peer pre-shared key matching
19.16.19.136
032204: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload
032205: May 20 12:01:03.529 EDT: ISAKMP:(1113): vendor ID is Unity
032206: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload
032207: May 20 12:01:03.529 EDT: ISAKMP:(1113): vendor ID seems Unity/DPD but
major 9 mismatch
032208: May 20 12:01:03.529 EDT: ISAKMP:(1113): vendor ID is XAUTH
032209: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload
032210: May 20 12:01:03.529 EDT: ISAKMP:(1113): speaking to another IOS box!
032211: May 20 12:01:03.529 EDT: ISAKMP:(1113): processing vendor id payload
032212: May 20 12:01:03.529 EDT: ISAKMP:(1113):vendor ID seems Unity/DPD but
hash mismatch
032213: May 20 12:01:03.529 EDT: ISAKMP:received payload type 20
032214: May 20 12:01:03.529 EDT: ISAKMP (1113): His hash no match - this node
outside NAT
032215: May 20 12:01:03.529 EDT: ISAKMP:received payload type 20
032216: May 20 12:01:03.529 EDT: ISAKMP (1113): No NAT Found for self or peer
032217: May 20 12:01:03.529 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_MAIN_MODE
032218: May 20 12:01:03.529 EDT: ISAKMP:(1113):Old State = IKE_I_MM4 New
State = IKE_I_MM4
032219: May 20 12:01:03.533 EDT: ISAKMP:(1113):Send initial contact
032220: May 20 12:01:03.533 EDT: ISAKMP:(1113):SA is doing pre-shared key
authentication using id type ID_IPV4_ADDR
032221: May 20 12:01:03.533 EDT: ISAKMP (1113): ID payload
next-payload : 8
type : 1
address : 19.24.11.142
protocol : 17
port : 500
length : 12
032222: May 20 12:01:03.533 EDT: ISAKMP:(1113):Total payload length: 12
032223: May 20 12:01:03.533 EDT: ISAKMP:(1113): sending packet to
19.16.19.136 my_port 500 peer_port 500 (I) MM_KEY_EXCH
032224: May 20 12:01:03.533 EDT: ISAKMP:(1113):Sending an IKE IPv4 Packet.
032225: May 20 12:01:03.533 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_COMPLETE
032226: May 20 12:01:03.533 EDT: ISAKMP:(1113):Old State = IKE_I_MM4 New
State = IKE_I_MM5
032227: May 20 12:01:03.561 EDT: ISAKMP (1113): received packet from
19.16.19.136 dport 500 sport 500 Global (I) MM_KEY_EXCH
032228: May 20 12:01:03.561 EDT: ISAKMP:(1113): processing ID payload. message
ID = 0
032229: May 20 12:01:03.561 EDT: ISAKMP (1113): ID payload
next-payload : 8
type : 1
address : 19.16.19.136
protocol : 17
port : 0
length : 12
032230: May 20 12:01:03.561 EDT: ISAKMP:(0):: peer matches *none* of the
profiles
032231: May 20 12:01:03.561 EDT: ISAKMP:(1113): processing HASH payload.
message ID = 0
032232: May 20 12:01:03.561 EDT: ISAKMP:received payload type 17
032233: May 20 12:01:03.561 EDT: ISAKMP:(1113): processing vendor id payload
032234: May 20 12:01:03.561 EDT: ISAKMP:(1113): vendor ID is DPD
032235: May 20 12:01:03.561 EDT: ISAKMP:(1113):SA authentication status:
authenticated
032236: May 20 12:01:03.561 EDT: ISAKMP:(1113):SA has been authenticated with
19.16.19.136
032237: May 20 12:01:03.561 EDT: ISAKMP: Trying to insert a peer
19.24.11.142/19.16.19.136/500/, and inserted successfully 313D3120.
032238: May 20 12:01:03.561 EDT: ISAKMP:(1113):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032239: May 20 12:01:03.561 EDT: ISAKMP:(1113):Old State = IKE_I_MM5 New
State = IKE_I_MM6
032240: May 20 12:01:03.561 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_MAIN_MODE
032241: May 20 12:01:03.561 EDT: ISAKMP:(1113):Old State = IKE_I_MM6 New
State = IKE_I_MM6
032242: May 20 12:01:03.561 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL,
IKE_PROCESS_COMPLETE
032243: May 20 12:01:03.561 EDT: ISAKMP:(1113):Old State = IKE_I_MM6 New
State = IKE_P1_COMPLETE
032244: May 20 12:01:03.561 EDT: ISAKMP:(1113):beginning Quick Mode exchange,
M-ID of 2581849008
032245: May 20 12:01:03.565 EDT: ISAKMP:(1113):QM Initiator gets spi
032246: May 20 12:01:03.565 EDT: ISAKMP:(1113): sending packet to
19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE
032247: May 20 12:01:03.565 EDT: ISAKMP:(1113):Sending an IKE IPv4 Packet.
032248: May 20 12:01:03.565 EDT: ISAKMP:(1113):Node 2581849008, Input =
IKE_MESG_INTERNAL, IKE_INIT_QM
032249: May 20 12:01:03.565 EDT: ISAKMP:(1113):Old State = IKE_QM_READY New
State = IKE_QM_I_QM1
032250: May 20 12:01:03.565 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL,
IKE_PHASE1_COMPLETE
032251: May 20 12:01:03.565 EDT: ISAKMP:(1113):Old State = IKE_P1_COMPLETE
New State = IKE_P1_COMPLETE
032252: May 20 12:01:03.597 EDT: ISAKMP (1113): received packet from
19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE
032253: May 20 12:01:03.597 EDT: ISAKMP: set new node 1341887425 to QM_IDLE
032254: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing HASH payload.
message ID = 1341887425
032255: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing NOTIFY
PROPOSAL_NOT_CHOSEN protocol 3
spi 0, message ID = 1341887425, sa = 0x30038454
032256: May 20 12:01:03.597 EDT: ISAKMP:(1113):deleting node 1341887425 error
FALSE reason "Informational (in) state 1"
032257: May 20 12:01:03.597 EDT: ISAKMP:(1113):Input = IKE_MESG_FROM_PEER,
IKE_INFO_NOTIFY
032258: May 20 12:01:03.597 EDT: ISAKMP:(1113):Old State = IKE_P1_COMPLETE
New State = IKE_P1_COMPLETE
032259: May 20 12:01:03.597 EDT: ISAKMP (1113): received packet from
19.16.19.136 dport 500 sport 500 Global (I) QM_IDLE
032260: May 20 12:01:03.597 EDT: ISAKMP: set new node 1837926342 to QM_IDLE
032261: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing HASH payload.
message ID = 1837926342
032262: May 20 12:01:03.597 EDT: ISAKMP:received payload type 18
032263: May 20 12:01:03.597 EDT: ISAKMP:(1113):Processing delete with reason
payload
032264: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete doi = 1
032265: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete protocol id = 1
032266: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete spi_size = 16
032267: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete num spis = 1
032268: May 20 12:01:03.597 EDT: ISAKMP:(1113):delete_reason = 10
032269: May 20 12:01:03.597 EDT: ISAKMP:(1113): processing DELETE_WITH_REASON
payload, message ID = 1837926342, reason: Unknown delete reason!
032270: May 20 12:01:03.597 EDT: ISAKMP:(1113):peer does not do paranoid
keepalives.
032271: May 20 12:01:03.597 EDT: ISAKMP:(1113):deleting SA reason "IKE SA
Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136)
032272: May 20 12:01:03.597 EDT: ISAKMP:(1113):deleting node 1837926342 error
FALSE reason "Informational (in) state 1"
032273: May 20 12:01:03.601 EDT: ISAKMP: set new node -577632662 to QM_IDLE
032274: May 20 12:01:03.601 EDT: ISAKMP:(1113): sending packet to
19.16.19.136 my_port 500 peer_port 500 (I) QM_IDLE
032275: May 20 12:01:03.601 EDT: ISAKMP:(1113):Sending an IKE IPv4 Packet.
032276: May 20 12:01:03.601 EDT: ISAKMP:(1113):purging node -577632662
032277: May 20 12:01:03.601 EDT: ISAKMP:(1113):Input = IKE_MESG_INTERNAL,
IKE_PHASE1_DEL
032278: May 20 12:01:03.601 EDT: ISAKMP:(1113):Old State = IKE_P1_COMPLETE
New State = IKE_DEST_SA
032279: May 20 12:01:03.601 EDT: ISAKMP:(1113):deleting SA reason "IKE SA
Lifetime Exceeded" state (I) QM_IDLE (peer 19.16.19.136)
032280: May 20 12:01:03.601 EDT: ISAKMP: Unlocking peer struct 0x313D3120 for
isadb_mark_sa_deleted(), count 0
032281: May 20 12:01:03.601 EDT: ISAKMP: Deleting peer node by peer_reap for
19.16.19.136: 313D3120
032282: May 20 12:01:03.601 EDT: ISAKMP:(1113):deleting node -1713118288 error
FALSE reason "IKE deleted"
032283: May 20 12:01:03.601 EDT: ISAKMP:(1113):Input = IKE_MESG_FROM_PEER,
IKE_MM_EXCH
032284: May 20 12:01:03.601 EDT: ISAKMP:(1113):Old State = IKE_DEST_SA New
State = IKE_DEST_SA
R1-IPSEC1#
032285: May 20 12:01:03.601 EDT: IPSEC(key_engine): got a queue event with 1
KMI message(s)
R1-IPSEC1#
032286: May 20 12:01:23.601 EDT: ISAKMP:(1112):purging node 497356209
032287: May 20 12:01:23.605 EDT: ISAKMP:(1112):purging node 309704327
032288: May 20 12:01:23.605 EDT: ISAKMP:(1112):purging node -472341339
R1-IPSEC1#
032289: May 20 12:01:33.441 EDT: IPSEC(key_engine): request timer fired: count
= 2,
(identity) local= 19.24.11.142:0, remote= 19.16.19.136:0,
local_proxy= 19.24.11.59/255.255.255.255/0/0 (type=1),
remote_proxy= 19.16.19.158/255.255.255.255/0/0 (type=1)
032290: May 20 12:01:33.605 EDT: ISAKMP:(1112):purging SA., sa=2A271B9C,
delme=2A271B9C
R1-IPSEC1#
032291: May 20 12:01:53.597 EDT: ISAKMP:(1113):purging node 1341887425
032292: May 20 12:01:53.597 EDT: ISAKMP:(1113):purging node 1837926342
032293: May 20 12:01:53.601 EDT: ISAKMP:(1113):purging node -1713118288
R1-IPSEC1#
032294: May 20 12:02:03.601 EDT: ISAKMP:(1113):purging SA., sa=30038454,
delme=30038454
R1-IPSEC1#
|
Since remote site is customer site which the configuration is not able to check. But customer confirmed the vpn tunnel is able to built when initiated from their end. It seems phase 1 and phase 2 configuration should be right since tunnel can be built.
There is similar post regarding this issue "Cisco IOS VPN Error: Peer Does Not Do Paranoid Keepalives"
Here are some good explanation about the error message "peer does not do paranoid keepalives"
I see this router going through each of the MM states.
IKE_I_MM2 –> IKE_I_MM3 –> IKE_I_MM4 –> IKE_I_MM5 –> IKE_I_MM6 –> QM_IDLE
This looks great. It’s completing the entire Phase one key exchange process. So I know nothing is wrong with my ISAKMP settings.
Shortly after it becomes QM_IDLE it starts deleting SAs and says:
ISAKMP:(9577):peer does not do paranoid keepalives.Basically, after P1 completed, P2 failed will have following reasons:
1. PFS configuration is not consistent on both ends
2. IPSEC SA life time is not same on both ends
In my case, it was PFS group number did not matched in both end. Once group number corrected, tunnel was able to build without problem.






No comments:
Post a Comment